Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to search the difference between the start and...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How do I search the difference between the start and end timestamps for each command in my script log and timechart the duration for each one?
I have a script log that looks like:
2015-02-16.46.580761857 , cmd1 = Start time of if
2015-02-16.46.586912593 , cmd1 = end time of if
2015-02-16.46.588503884 , cmd2 = Start time of if
2015-02-16.46.589967322 , cmd2 = end time of if
2015-02-16.46.591767534 , cmd3 = Start time of grep
2015-02-16.46.595647254 , cmd3 = end time of grep
2015-02-16.46.597398658 , cmd4 = Start time of if
2015-02-16.46.598979442 , cmd4 = end time of if
2015-02-16.46.600440199 , cmd5 = Start time of sed command
2015-02-16.46.611868517 , cmd5 = end time of sed command
2015-02-16.46.613545578 , cmd6 = Start time of if
2015-02-16.46.614971442 , cmd6 = End time of if
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What with this?
※After that, please calculate the duration .
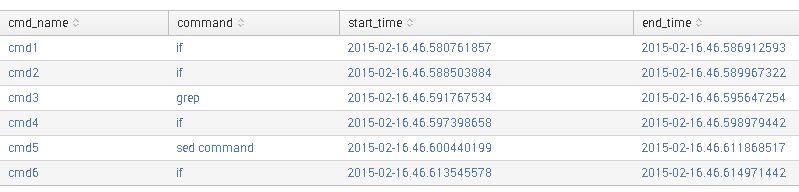
.....your search.....|rex field=_raw "^(?P<Time>[^ ]+)\s+,\s+(?P<cmd_name>\w+)\s+=\s+(?P<status>\w+\s+\w+) of (?P<command>.+)"|eval start_time=if(status="Start time",Time,"")|eval end_time=if(status="end time" OR status="End time",Time,"")|table cmd_name,command,start_time,end_time|stats max(start_time) as start_time,max(end_time) as end_time by cmd_name,command
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What with this?
※After that, please calculate the duration .
.....your search.....|rex field=_raw "^(?P<Time>[^ ]+)\s+,\s+(?P<cmd_name>\w+)\s+=\s+(?P<status>\w+\s+\w+) of (?P<command>.+)"|eval start_time=if(status="Start time",Time,"")|eval end_time=if(status="end time" OR status="End time",Time,"")|table cmd_name,command,start_time,end_time|stats max(start_time) as start_time,max(end_time) as end_time by cmd_name,command
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
.....your search.....|rex field=_raw "^(?P[^ ]+)\s+,\s+(?P\w+)\s+=\s+(?P\w+\s+\w+) of (?P.+)"|eval start_time=if(status="Start time",Time,"")|eval end_time=if(status="end time" OR status="End time",Time,"")|table cmd_name,command,start_time,end_time|stats max(start_time) as start_time,max(end_time) as end_time by cmd_name,command
THE ABOVE QUERIE NOT WORKING ANY ONE CAN HELP ME ON THIS QUESTION URGENT........
EITHER I HAVE TO ANY CONFIGURATION THAT I HAVE TO TAKE CONG FILE THAT SPEC OR EXAMPLE CONFG FILE PLEASE HELP ONTHIS