Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to remove unwanted row base on condition of co...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi, I am new in Splunk,
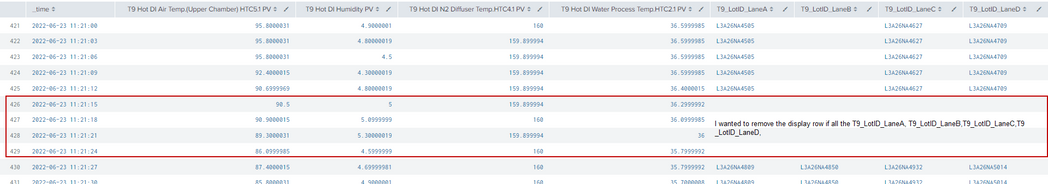
if I want to remove the display of all column field for T9_LotID_LaneA,T9_LotID_LaneB,T9_LotIB_LaneC,T9_LotID_LaneD, was empty or null value
my base search:
OWA03 AND ID = "T9 Hot DI Air Temp.(Upper Chamber) HTC5.1 PV" OR ID = "T9 Hot DI Humidity PV" OR ID = "T9 Hot DI N2 Diffuser Temp.HTC4.1 PV" OR ID = "T9 Hot DI Water Process Temp.HTC2.1 PV" OR ID = "T9_LotID_LaneA" OR ID = "T9_LotID_LaneB" OR ID = "T9_LotID_LaneC" OR ID = "T9_LotID_LaneD"
|timechart span=3s cont=false latest(Value) by ID
the results:
please advise ,
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, these fields hold non-numerics (strings) so comparing to "0" makes more sense although perhaps using != "" would be more appropriate?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
it work well now. Thanks for the help.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
below is the column field that I want to filter:
(((ID = "T9_LotID_LaneA" AND Value >0 AND Value!="03_Dummy")) OR ((ID = "T9_LotID_LaneB" AND Value >0 AND Value!="03_Dummy")) OR ((ID = "T9_LotID_LaneC" AND Value >0 AND Value!="03_Dummy")) OR ((ID = "T9_LotID_LaneD" AND Value >0 AND Value!="03_Dummy")))
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try something like this
OWA03 AND ID = "T9 Hot DI Air Temp.(Upper Chamber) HTC5.1 PV" OR ID = "T9 Hot DI Humidity PV" OR ID = "T9 Hot DI N2 Diffuser Temp.HTC4.1 PV" OR ID = "T9 Hot DI Water Process Temp.HTC2.1 PV" OR ID = "T9_LotID_LaneA" OR ID = "T9_LotID_LaneB" OR ID = "T9_LotID_LaneC" OR ID = "T9_LotID_LaneD"
|timechart span=3s cont=false latest(Value) by ID
| where (T9_LotID_LaneA >0 AND T9_LotID_LaneA !="03_Dummy") OR (T9_LotID_LaneB >0 AND T9_LotID_LaneB !="03_Dummy") OR (T9_LotID_LaneC >0 AND T9_LotID_LaneC !="03_Dummy") OR (T9_LotID_LaneD >0 AND T9_LotID_LaneD !="03_Dummy")- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi ITWhisperer,
Thank you for your help.
the result : show empty. but after I change from >0 to >" 0" it show the results. What does it mean from >0 to >"0" is it for integer value and string value ?
OWA03 AND ID = "T9 Hot DI Air Temp.(Upper Chamber) HTC5.1 PV" OR ID = "T9 Hot DI Humidity PV" OR ID = "T9 Hot DI N2 Diffuser Temp.HTC4.1 PV" OR ID = "T9 Hot DI Water Process Temp.HTC2.1 PV" OR ID = "T9_LotID_LaneA" OR ID = "T9_LotID_LaneB" OR ID = "T9_LotID_LaneC" OR ID = "T9_LotID_LaneD"
|timechart span=3s cont=false latest(Value) by ID
| where (T9_LotID_LaneA >"0" AND T9_LotID_LaneA !="03_Dummy") OR (T9_LotID_LaneB >"0" AND ID.T9_LotID_LaneB !="03_Dummy") OR (T9_LotID_LaneC >"0" AND T9_LotID_LaneC !="03_Dummy") OR (T9_LotID_LaneD >"0" AND T9_LotID_LaneD !="03_Dummy")
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, these fields hold non-numerics (strings) so comparing to "0" makes more sense although perhaps using != "" would be more appropriate?