Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to extract a field from my raw data using rex?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Below is my raw logs.
I want to extract "analystVerdict" & its corresponding result from raw logs. can someone please help
\"mitigationStartedAt\": \"2022-04-13T03:57:58.393000Z\", \"status\": \"success\"}], \"threatInfo\": {\"analystVerdict\": \"false_positive\", \"analystVerdictDescription\": \"False positive\", \"automaticallyResolved\": false, \"browserType\": null, \"certificateId\": \"\", \"classification\": \"Malware\",
I tried below. But i am failing to get the result
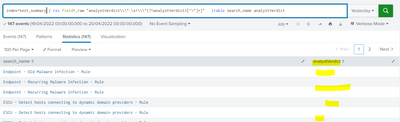
index=test_summary | rex field=_raw ":\\\"(?<analystVerdict>\w+)\\\"" |table search_name analystVerdict
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
| rex "analystVerdict\\\\\":\s+\\\\\"(?<analystVerdictDescription>[^\\\\\"]+)"- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
| rex "analystVerdict\\\\\":\s+\\\\\"(?<analystVerdictDescription>[^\\\\\"]+)"- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @alexspunkshell,
please try this regex:
| rex "analystVerdictDescription\\\":\s+\\\"(?<analystVerdictDescription>[^\"]+)"that you can test at https://regex101.com/r/IjwJYM/1
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@gcusello Thanks for your help
I tried but the field is empty in my results. But the raw logs is having the values.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @alexspunkshell,
sometimes I found a behaviour in Splunk different than regex101, so please try this:
| rex "analystVerdictDescription\\\\":\s+\\\\"(?<analystVerdictDescription>[^\"]+)"Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Still the same
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content