Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to do timechart on a field that has same name ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I have a log with a field call "Event_Types" and then another field call "Alert Level" .
In my logs there is an event call "Ping" but this "Ping" has 2 Alert Levels 6 and 10.
I want to do a timechart on Event_Types but also want to show that there are 2 pings with different alert levels counted over time. How should I search for it?
Alert_Level > 6 | timechart count(Event_Types) as Event_Types count(Alert_Level) will show "The argument 'count(Alert_Level)' is invalid."
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Give this a try
Updated: Fixed typo with field name
your base search | eval EventType=Event_Types.":".Alert_Level | timechart count by EventType
OR
your base search | where Alert_Level > 6 | eval EventType=Event_Types.":".Alert_Level | timechart count by EventType
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
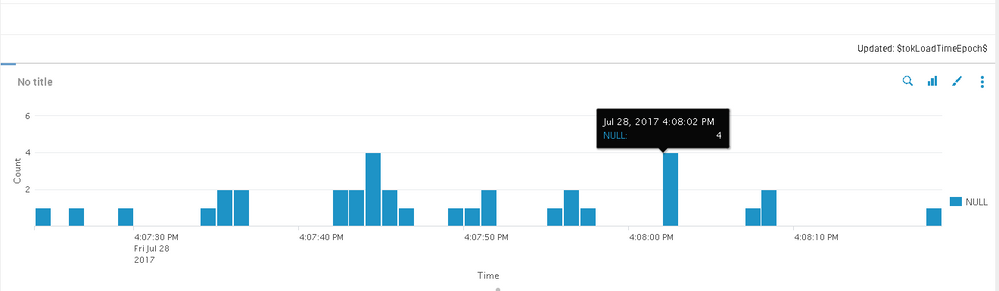
@wuming79, there was a typo in my original answer (thanks @niketnilay for pointing that one out), which may be causing that NULL column name. Try the updated answer.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Give this a try
Updated: Fixed typo with field name
your base search | eval EventType=Event_Types.":".Alert_Level | timechart count by EventType
OR
your base search | where Alert_Level > 6 | eval EventType=Event_Types.":".Alert_Level | timechart count by EventType
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@somesoni2, I think field name is Event_Types and not Event_Type.
@wuming79, can you please confirm the field names Event_Types and Alert_Level?
| makeresults | eval message= "Happy Splunking!!!"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi, it's working now. Thanks! 🙂
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are you trying a query like the following?
| where Alert_Level > 6 | timechart count(Event_Types) as Event_Types count(Alert_Level) as Alert_Level
| makeresults | eval message= "Happy Splunking!!!"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi sorry, I made a mistake, I need it to display "|Alert_Level > 6 | timechart count(Event_Types) by Event_Types count(Alert_Level) "