Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to create a new field:value pair based on valu...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to create a new field:value pair based on values of another field?
Hi,
From our IDS logs, we have a field named "blocked" where value is 0 for allowed and 1 for blocked. How can I create another field named action, which should have value of ("allowed" / "blocked") based on the values in the original 'blocked' field?
So, if event has blocked=0, then action=allowed.
Also, since this is for a CIM Data model having something permanent would be nice.
one way I could think of is to create a field alias for blocked -> action, and then add a lookup table file for this new alias mapping 0 -> allowed and 1 -> blocked.
Is there any better way to achieve this?
Thanks,
~ Abhi
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Giuseppe,
Looks like blocked is getting a 3rd value for '2' as well, so instead of a 'if' I ended up using a 'case', which works like a charm when testing in a search.
eval action=case(blocked=0, "allowed",blocked=1,"blocked", blocked=2, "would be blocked")
But when I created a calculated field, it did not appear in the search. Also, the original 'blocked' field disappeared as well. Not sure what could have cause this to happen. Once I deleted this calculated field, 'blocked' re-appeared in the searches.
I made sure permissions are global(read for all and write for admin) and allowed for all applications. Just to put it out there, I am working on a 3 node SH cluster and logged in via a LB Virtual URL Not sure if that has anything to do with this.
Thanks,
~ Abhi
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
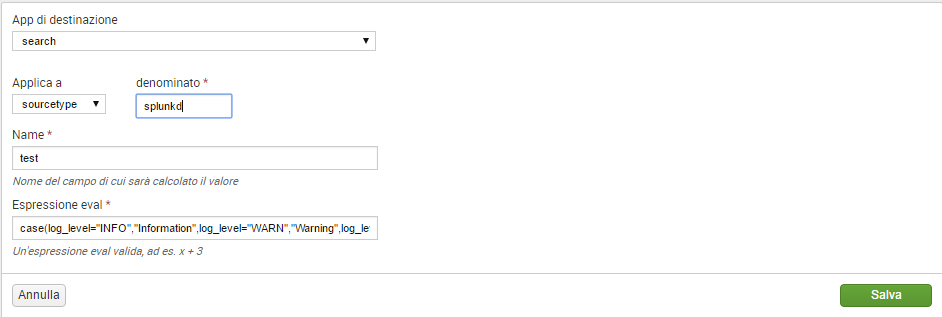
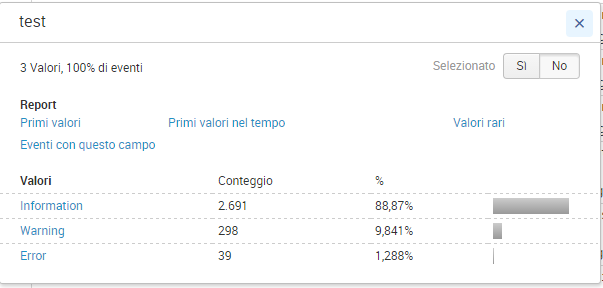
Hi abhijittikekar,
I don't think that LB or SH Cluster is a problem.
At first I suggest to wait for a few minutes, because there's usually a delay in fields displaying (I never understood why!).
After, verify that you're using the correct sourcetype.
Every way, as you can see in the attached screenshots, on my Splunk it runs (sorry for the italian interface).
Bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
no luck yet.. 😞
Re-created the action field and it's been 2 days since then. Original blocked field still functions as expected but calculated field "action" is nowhere to be seen.
There are no other conflicting extractions for 'action' under props.conf
# cat /opt/splunk/etc/apps/Splunk_TA_sourcefire/local/props.conf
[eStreamer]
FIELDALIAS-estreamer_dvc_SF = sensor AS dvc
FIELDALIAS-estreamer_category_SF = class_desc AS category
FIELDALIAS-estreamer_dest_SF = dest_ip AS dest
FIELDALIAS-estreamer_src_SF = src_ip AS src
FIELDALIAS-estreamer_severity_SF = priority AS severity
FIELDALIAS-severity_id_for_estreamer = priority AS severity_id
EVAL-action = action=case(blocked=0, "allowed",blocked=1,"blocked", blocked=2, "would be blocked")
[estreamer]
Not sure what else to check here. Have opened a support case for this and will revert back as soon as we solve it.
Thanks,
~ Abhi
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Very strange, as you can see, in my test it works.
tell me how Support will answer!
Bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
And here is the info on adding calculated fields in data models.
http://docs.splunk.com/Documentation/Splunk/6.5.2/Knowledge/Addanevalexpressionattribute