Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Splunk Search
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Correlation search
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Kitag345
Explorer
02-17-2023
09:27 AM
Hello,
I would like to request guidance on how to create a correlation search based on data provided by SANS Threat Intelligence from https://isc.sans.edu/block.txt
The malicious IPs from "block.txt" are updated regularly. How can my correlation search track that change in real-time? What queries to use?
Notes: The SANS Threat Intel has already been enabled.
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
nyc_jason

Splunk Employee
02-17-2023
09:43 AM
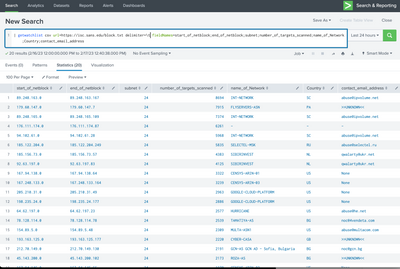
consider using the PAVO Getwatchlist add-on, then you can do this:
Or for performance, schedule the search every 30min, and pipe it to a lookup. then run your search using the lookup for matches.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
nyc_jason

Splunk Employee
02-17-2023
09:43 AM
consider using the PAVO Getwatchlist add-on, then you can do this:
Or for performance, schedule the search every 30min, and pipe it to a lookup. then run your search using the lookup for matches.
Get Updates on the Splunk Community!
Modern way of developing distributed application using OTel
Recently, I had the opportunity to work on a complex microservice using Spring boot and Quarkus to develop a ...
Enterprise Security Content Update (ESCU) | New Releases
Last month, the Splunk Threat Research Team had 3 releases of new security content via the Enterprise Security ...
Archived Metrics Now Available for APAC and EMEA realms
We’re excited to announce the launch of Archived Metrics in Splunk Infrastructure Monitoring for our customers ...