Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Splunk Search
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to create a correlation search based on data p...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Kitag345
Explorer
02-17-2023
09:27 AM
Hello,
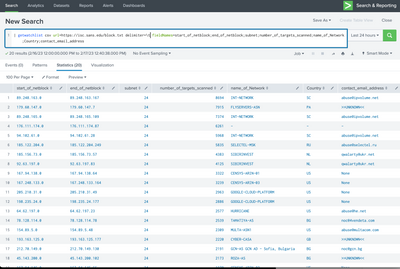
I would like to request guidance on how to create a correlation search based on data provided by SANS Threat Intelligence from https://isc.sans.edu/block.txt
The malicious IPs from "block.txt" are updated regularly. How can my correlation search track that change in real-time? What queries to use?
Notes: The SANS Threat Intel has already been enabled.
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
nyc_jason

Splunk Employee
02-17-2023
09:43 AM
consider using the PAVO Getwatchlist add-on, then you can do this:
Or for performance, schedule the search every 30min, and pipe it to a lookup. then run your search using the lookup for matches.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
nyc_jason

Splunk Employee
02-17-2023
09:43 AM
consider using the PAVO Getwatchlist add-on, then you can do this:
Or for performance, schedule the search every 30min, and pipe it to a lookup. then run your search using the lookup for matches.
Get Updates on the Splunk Community!
Enterprise Security Content Update (ESCU) | New Releases
In December, the Splunk Threat Research Team had 1 release of new security content via the Enterprise Security ...
Why am I not seeing the finding in Splunk Enterprise Security Analyst Queue?
(This is the first of a series of 2 blogs).
Splunk Enterprise Security is a fantastic tool that offers robust ...
Index This | What are the 12 Days of Splunk-mas?
December 2024 Edition
Hayyy Splunk Education Enthusiasts and the Eternally Curious!
We’re back with another ...