Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to change default permissions for lookups?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to change default permissions for lookups?
I'm wondering if there's a way to change the behavior of how Splunk applies permissions to lookups generated via | outputlookup?
Currently, if user SplunkA generates a lookup on data in IndexA, by default the lookup gets the permissions of the app it's being generated in. If user SplunkB is in a role that doesn't have access to IndexA, he now potentially has access to partial (or full) data that exists in IndexA by looking at that lookup (via |inputlookup or the Data Sets tab).
Is it possible to force user generated lookups to be private by default? Then, we can have an elevated user evaluate if they are appropriate to be shared globally, and then assign the correct role permissions at that time.
We are running Splunk 6.5.2.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did you get an answer for this? I am also looking to change the default behavior of how lookups are created. A few years back I believe the default behavior was to create the lookup as a private object under the user's app directory... which was way better for object management.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello coltwagner,
lookups are not in an index, when lookups are generated they are global and can be seen by all users.
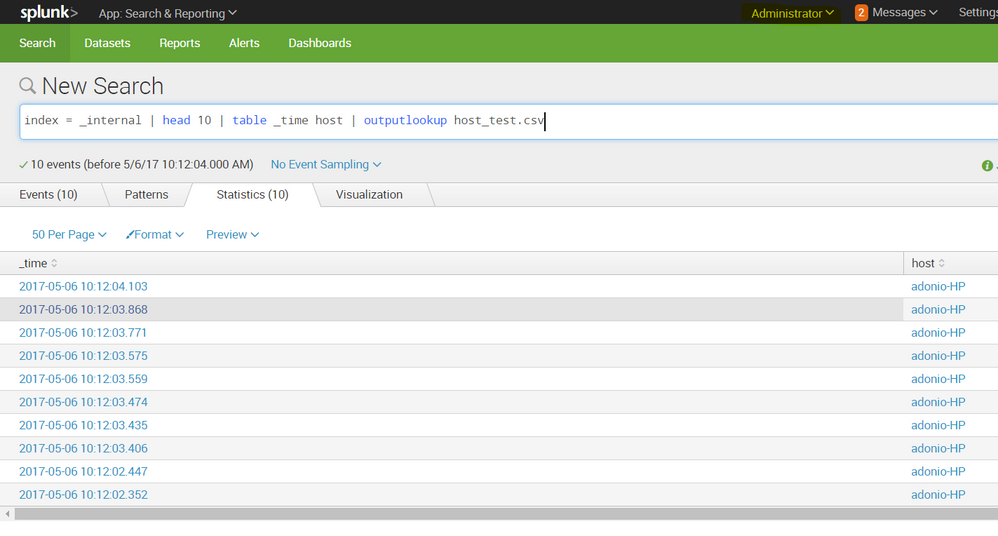
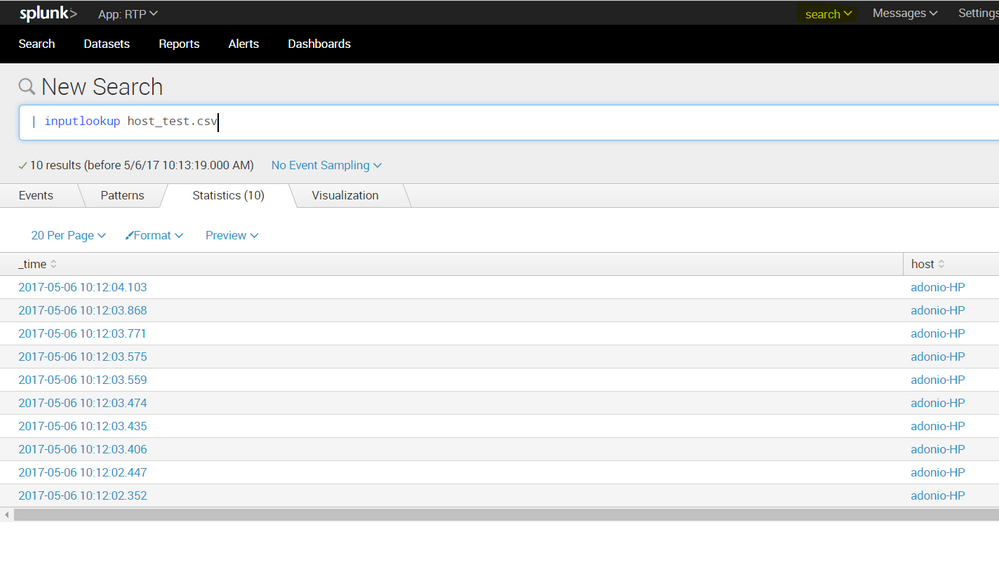
examples are in screenshot as I cerated a lookup with the admin account under search app and searched this lookup with a different user (limited privileges) under a different app.
for the second part of your question, here is a good answer by @DalJeanis and @somesoni2 that summarizes it:
https://answers.splunk.com/answers/521382/can-we-create-outputlookup-table-user-based.html