Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How do I write the regex to identify the sourceip ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
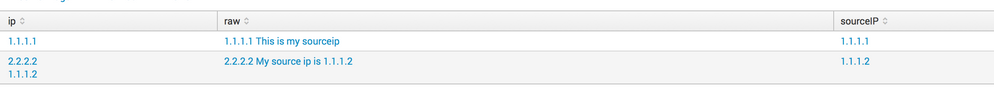
I have logs like below
1.1.1.1 This is my sourceip
2.2.2.2 My source ip is 1.1.1.2
I have a situation where in some events, my sourceip comes first in the line (AS in First EVENT), and other events, IPs come first, but this is not sourceip. Whatever comes after (in this case, 1.1.1.2) is my source ip. How to write a regex for this lookahead?
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try this:
| rex field=_raw max_match=0 "(?<ip>\d{1,3}\.\d{1,3}\.\d{1,3}\.\d{1,3})"
| eval sourceIP = mvindex(ip, mvcount(ip)-1)
This is basically going to do the following:
- Store all the IPs in your event in the ip multivalued field (even if there's only one match, it will be a multivalued field with one value only)
- Retrieve the latest ip from the multivalued field and assign to sourceIP
Example:
| stats count | fields - count
| eval raw = "1.1.1.1 This is my sourceip; 2.2.2.2 My source ip is 1.1.1.2"
| eval raw = split(raw, ";")
| mvexpand raw
| rex field=raw max_match=0 "(?<ip>\d{1,3}\.\d{1,3}\.\d{1,3}\.\d{1,3})"
| eval sourceIP = mvindex(ip, mvcount(ip)-1)
Output: see attached picture
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try this:
| rex field=_raw max_match=0 "(?<ip>\d{1,3}\.\d{1,3}\.\d{1,3}\.\d{1,3})"
| eval sourceIP = mvindex(ip, mvcount(ip)-1)
This is basically going to do the following:
- Store all the IPs in your event in the ip multivalued field (even if there's only one match, it will be a multivalued field with one value only)
- Retrieve the latest ip from the multivalued field and assign to sourceIP
Example:
| stats count | fields - count
| eval raw = "1.1.1.1 This is my sourceip; 2.2.2.2 My source ip is 1.1.1.2"
| eval raw = split(raw, ";")
| mvexpand raw
| rex field=raw max_match=0 "(?<ip>\d{1,3}\.\d{1,3}\.\d{1,3}\.\d{1,3})"
| eval sourceIP = mvindex(ip, mvcount(ip)-1)
Output: see attached picture
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can use two different regex:
for the first event: rex field=yourfield "^(?P(\d.){4})This is my sourceip"
for the 2nd even: rex field=youfield ".*My source ip is\s(?P(\d.){3}\d)"