Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How do I filter string values from a greater-than-...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
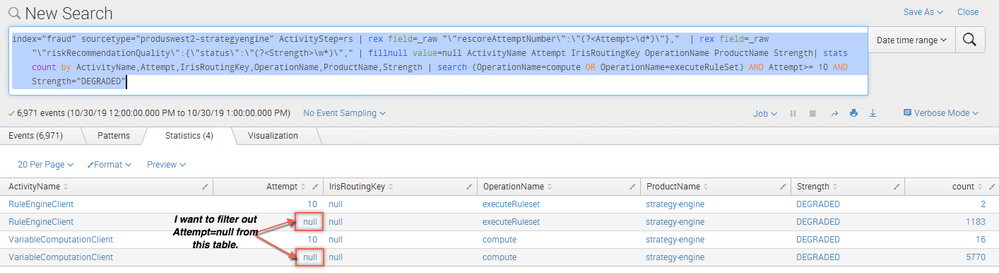
How do I filter string values from a greater-than-or-equal-to numerical comparison?
I have a field in my query called Attempt that is either a non-negative integer or a special value "null". I use the special "null" string value because I am creating a summary query and don't want to lose events for which fields aren't present. I therefore use the fillnull operator that you can see in the query below:
index="fraud" sourcetype=strategy-engine ActivityStep=rs
| rex field=_raw "\"rescoreAttemptNumber\":\"(?<Attempt>\d*)\"},"
| rex field=_raw "\"riskRecommendationQuality\":{\"status\":\"(?<Strength>\w*)\","
| fillnull value=null ActivityName Attempt IrisRoutingKey OperationName ProductName Strength
| stats count by ActivityName,Attempt,IrisRoutingKey,OperationName,ProductName,Strength
| search (OperationName=compute OR OperationName=executeRuleSet) AND Attempt>= 10 AND Strength="DEGRADED"
My problem is really the Attempt>=10 term because I see both "null" and "10" values in my results table. My table returned is the table below:
Ideally, I would like to filter such results where Attempt=null without using the term Attempt>=10 AND Attempt!=null because the first part of the query (up to and including the stats operator) is actually a new general-purpose summary query. I suspect that people using this summary query will often forget to use the Attempt!="null" and just end up with extraneous results if I require them to use this term.
Is there any way to get Splunk to filter out non-numerical values from a LHS>=RHS style-comparison? Your help would be greatly appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@entpnerd ,
Try using where for comparison which should filter out the result >=10 ignoring the null
What goes around comes around. If it helps, hit it with Karma 🙂