Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Events Indexed Only For Specific Days
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Events Indexed Only For Specific Days
Hi all,
I have configured Splunk to poll a REST API to pull certain events. The message is in JSON format, and after configuring the appropriate Data Input and updating the props.conf file, I can see the events in Splunk being parsed correctly.
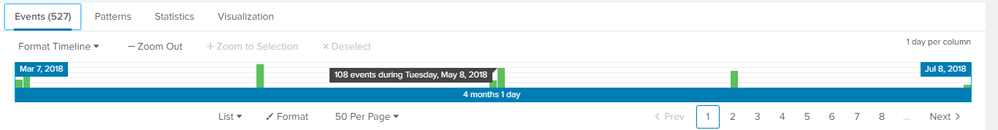
However, I noticed that only events for the 7th and the 8th of each month are being indexed, or at the very minimum, displayed. If you look at the screenshot, you can see that there are no events between the 9th of each month and the 6th of the following month.
"Event Sampling" is not selected, and when I select a specific time range (say "Last 7 days" or "All time") I only see events for those 2 days of the month. I am using Splunk Enterprise 7.1.1 with both Chrome 67.0.3396.99 and Internet Explorer 11.1155.15063.
Is there a way to check whether those events have actually been retrieved in Splunk but they are not displayed, or whether those events are not in Splunk at all?
Thank you
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Check your TIME_FORMAT setting. Also check your index=_* for error logs related to your sourcetype. If your TIME_FORMAT is wrong (or not being applied; did you send it to your Indexers and restart them there?) your events could be being timestamped too var in the past ( MAX_DAYS_AGO ) or the future ( MAX_DAYS_HENCE) causing Splunk to deliberately thrown them away (it logs this).
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Perhaps you could provide your search string? My guess would be that the data is only there as you see it. It may be helpful to see some events as they are returned as well.