Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- EVAL separate search for Monday
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Each Monday the event count for skypeuk is 30 and skypeus is 200. However, for the rest of the weekday skypeuk is atleast is 290 and skypeus is 700.
How would I build in a new search to the one below to accommodate this low event count on Monday?
| tstats count as "Data Received" where index=msexchange host=opspkhf03p source=skypeuk
| eval result=if('Data Received'> 200, "PASS", "FAIL")
| eval host="opspkhf03p"
| append
[| tstats count as "Data Received" where index=msexchange host=opspkhf03p source=skypeus
| eval result=if('Data Received'> 700, "PASS", "FAIL")
| eval host="opspkhf03p"]
| table host, "Data Received", result
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
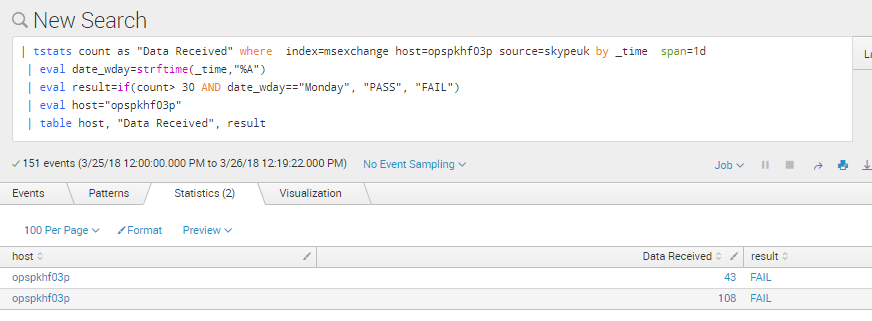
You can do the tstats by _time and then evaluate if it is a Monday or not:
| tstats count where index=_internal by _time span=1d
| eval date_wday=strftime(_time,"%A")
| eval result=if(count> 700 AND date_wday=="Monday", "PASS", "FAIL")
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That is happening because your search is also going through the 25th of March which is Sunday.
If in the end you put the date_wday in the table you will get one row for Sunday and another for Monday.
If you just want the data for Monday, then just filter that one out like I;m showing below. If not, just have the results per date_wday where you can see Monday results but also any other days you want. It is up to you.
| tstats count as "Data Received" where index=msexchange host=opspkhf03p source=skypeuk by _time span =1d
| eval date_wday=strftime(_time,"%A")
| where date_wday=="Monday"
| eval result=if(count> 30 AND date_wday=="Monday", "PASS", "FAIL")
| eval host="opspkhf03p"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can do the tstats by _time and then evaluate if it is a Monday or not:
| tstats count where index=_internal by _time span=1d
| eval date_wday=strftime(_time,"%A")
| eval result=if(count> 700 AND date_wday=="Monday", "PASS", "FAIL")
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for this. I ran this but it is saying fail with the below search. When adding date_wday to the table it has no value.
| tstats count as "Data Received" where index=msexchange host=opspkhf03p source=skypeuk
| eval date_wday=strftime(_time,"%A")
| eval result=if(count> 30 AND date_wday=="Monday", "PASS", "FAIL")
| eval host="opspkhf03p"
| append
[| tstats count as "Data Received" where index=msexchange host=opspkhf03p source=skypeus
| eval date_wday=strftime(_time,"%A")
| eval result=if(count> 200 AND date_wday=="Monday", "PASS", "FAIL")
| eval host="opspkhf03p"]
| table host, "Data Received", result
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you very much, this worked!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes because your did not put the tstats by _time
| tstats count where index=_internal by _time span=1d
| eval date_wday=strftime(_time,"%A")
| eval result=if(count> 700 AND date_wday=="Monday", "PASS", "FAIL")
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How can I run
| tstats count where index=_internal by _time span=1d
with my first line
| tstats count as "Data Received" where index=msexchange host=opspkhf03p source=skypeuk
They don't run together. Am I explaining myself correctly?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
They can run together of you put it like this
| tstats count as "Data Received" where index=msexchange host=opspkhf03p source=skypeuk by _time span =1d
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey
What exactly do you want to achieve here?
What do you want to do with the Monday case? Is it different? Do you have different PASS/FAIL thresholds you want to have just for Mondays?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I would like for it to check if it is Monday and use the below pseudo-code logic
for skypeuk
If dayOfWeek=Monday
check if event count (Data Received) is greater than equals 290 then PASS else FAIL
for skypeus
If dayOfWeek=Monday
check if event count (Data Received) is greater than equals 700 then PASS else FAIL