Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Display all the results of two searches.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Display all the results of two searches.
Hi Experts,
I am running two searches by combining them with appendcols.
But the final result is the common fields of both the searches.
I want the entire search result of both the main and subsearch.
I am using stats as well.
Please advise.
Thank you.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @gcusello,
sourcetype=abc index=123
| spath _url
| search _url=US OR ASIA
|spath "_US_ version"
| stats dc(hostname) by US_ version
|rename US_ version as version
|appendcols [search sourcetype=abc index=123
| spath _url
| search _url=US OR ASIA
|spath "_ASIA_ version"
| stats dc(hostname) by ASIA_ version
|rename ASIA_ version as version
]
| stats sum(dc(hostname)) by version
Here i want the results of both US_version and ASIA_version. All the results int both the searches.
But now the problem is ,its displaying only the common version numbers.
Thank you.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @email2vamsi,
it's also possible to optimize this search without using append command (not the appendcols command): remeber that there's the limit of 50,000 results in subsearches.
But anyway, please try something like this:
sourcetype=abc index=123
| spath _url
| search _url=US OR _url=ASIA
| spath "_US_version"
| stats dc(hostname) AS US_count by US_version
| rename US_version as version
| eval type="US"
| appendcols [ search
sourcetype=abc index=123
| spath _url
| search _url=US OR _url=ASIA
| spath "_ASIA_version"
| stats dc(hostname) AS ASIA_count by ASIA_version
| rename ASIA_version as version
| eval type="ASIA"
]
| stats values(type) AS Type sum(US_count) AS US_count sum(ASIA_count) AS ASIA_count by version beware to one thing: I sow a space in the fields you used in spath commands, is this correct or not?
If you have a space in a field you have to use double quotes.
Then there's an error in the search command "search _url=US OR ASIA", you should use "search _url=US OR _url=ASIA"
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello @gcusello
Your query worked for me after changing it to append.
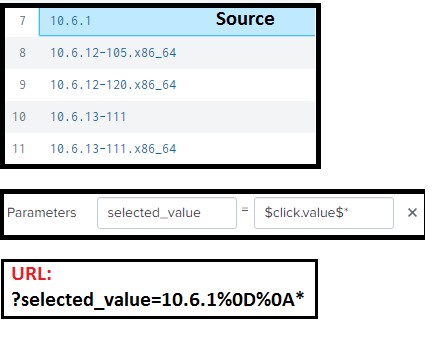
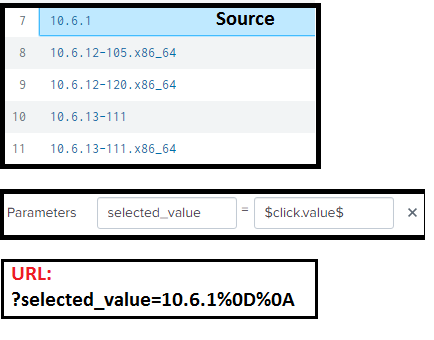
I have one more problem. For drill-down, I can see the following token in the URL.
selected_value=8.8.0%0D%0A*
Here %0D%0A means a space.
I just want to pass 8.8.0*, with out a space.
The rtrim in source dashboard is unable to trim the space at the end of 8.8.0.
Please suggest.
Thank you
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @email2vamsi,
this is another question, but anyway, can you share the drilldown row in dashboard source and the complete url?
Probably there's something in the drilldown row.
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In the target dashboard query comes like this, with * in the new line.
| search "_version"=10.6.1
*
If i do not use *, no rows is getting displayed.
If i move the * next to 10.6.1 (10.6.1*) , then the rows related to 10.6.1 are getting displayed, including 10.6.1,
10.6.12-105.x86_64,10.6.12-120.x86_64,10.6.13-111,10.6.13-111.x86_64
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @email2vamsi,
at first sight, I hint to insert "*" in the secondary dashboard and pass the token as is.
But, could you share the row of drilldown in the code?
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @gcusello
Version sum(Count)
1 30
2 8.8.0
3
3 10.2.2-1370.x86_64
2
4 10.5.1-1582.x86_64
1
5 10.5.5-106
28
6 10.5.5-106.x86_64
17
7 10.6.1
18
8 10.6.12-105.x86_64
19
9 10.6.12-120.x86_64
756
10 10.6.13-111
5
11 10.6.13-111.x86_64
1
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @email2vamsi,
sorry for the misunderstanding: id' like to see the code of the drilldown section:
open the source of your dashboard
share the drilldown sect6ion of the panel you're analyzing, you can recognize this part because is vetween the <drilldown> tags and similar to the following:
<drilldown>
<link target="_blank">/app/my_app/my_secondary_dashboard?earliest=$Time.earliest$&latest=$Time.latest$&my_token=$click.row$</link>
</drilldown>Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @gcusello
<drilldown>
<link target="_blank">/app/app_name/server_list?selected_value=$click.value$&location_tok2=$location_tok2$&Cust_id=$Cust_id$</link>
</drilldown>
Thank you.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @email2vamsi,
using this link you shouldn't have the "%0D%0A*".
As I said, if you need the "*" for the searches, put it in the secondary dashboard.
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @gcusello
I have moved the * to secondary dashboard.
The token in the URL of the secondary dashboard is like this :
?selected_value=10.6.1%0D%0A
In the secondary dashboard query comes like this, with * in the new line.
| search "_version"="10.6.1
*"
If i do not use *, no rows are getting displayed.
I have to move the * next to 10.6.1 (| search "_version"="10.6.1*") , then the rows related to 10.6.1 are getting displayed, including 10.6.1,
10.6.12-105.x86_64,10.6.12-120.x86_64,10.6.13-111,10.6.13-111.x86_64
The carriage return in secondary dashboard query is causing the query to fail.
I could not figure out from where the carriage return is coming from.
Thank you.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @email2vamsi,
extract the relevant part of your field using a regex in the main dashboard:
| rex field=selected_value "^(?<selected_value>\d+\.\d+\.\d+)In this way, you're sure that the field "selected_value" contains only the first three numbers of the IP.
If there's the possibility that the field could contain three or four numbers of the IP you could try this:
| rex field=selected_value "^(?<selected_value>(\d+\.\d+\.\d+)(\d+\.\d+\.\d+\.\d+))Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
append is a different command than append cols - works in a different way. So it's up to you to decide which mode of operation is proper for your needs.
And no, %OD%OA does not mean space. It's most probably \r\n