Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Concurrent Logins on multiple Linux servers
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello
I am trying to find users who have logged into more than one system within the last 30 minutes. I want to return a list of users who have logged into more than one system during that time frame.
The Stats function of the search does not seem to pull any results after finding all the login sessions after looking at job inspection. The stats function is suppose to find distinct users where hosts is greater than 1.
index ="Wawf" L_Action="New session" earliest=-30min latest=now
|stats dc(L_User) as users dc(Linux_Server) as hosts by L_User,Linux_Server
|where hosts>1 | table L_User, Linux_Server
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @pstephens93,
Since you are using both L_User and Linux_Server for group by stats cannot count. Try below query;
index ="Wawf" L_Action="New session" earliest=-30min latest=now
| stats values(Linux_Server) as Linux_Server dc(Linux_Server) as host_count by L_User
| where host_count>1
| table L_User, Linux_Server
If this reply helps you an upvote is appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I thought you have a field named Linux_Server field in the logs. Please try below;
index ="Wawf" L_Action="New session" earliest=-30min latest=now
| stats values(L_Server) as Linux_Server dc(L_Server) as host_count by L_User
| where host_count>1
| table L_User, Linux_Server
If this reply helps you an upvote is appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @pstephens93,
Since you are using both L_User and Linux_Server for group by stats cannot count. Try below query;
index ="Wawf" L_Action="New session" earliest=-30min latest=now
| stats values(Linux_Server) as Linux_Server dc(Linux_Server) as host_count by L_User
| where host_count>1
| table L_User, Linux_Server
If this reply helps you an upvote is appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the Help
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I tried the Search you suggested it seems like it is having an issue with this line of code
|where host_count>1
When I run the following Command I get
index="Wawf" L_Action="New session" earliest=-30min latest=now
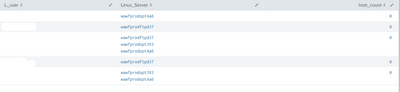
| stats values(L_Server) as Linux_Server dc(Linux_Server) as host_count by L_userI get a list of users who have logged into multiple servers and single servers during that time frame but host_count does not go above 0.
Any idea why that may be?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Question for you, This helps me find users who have logged into multiple systems within the last 30 minutes
index="Wawf" L_Action="New session" earliest=-30min latest=now
| stats values(L_Server) as Linux_Server dc(L_Server) as host_count by L_user
|where host_count > 1
How can I expand on this to track to see if the User logged off before logging into another system? Would that be a completely different search?
If user logs into server1 then logs into sever2 : this is a finding.
If user logs into server1, logs off, then logs into server2 : this is not a finding