Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Enterprise Security
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Premium Solutions
- :
- Splunk Enterprise Security
- :
- add variables into serach name
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
riqbal47010
Path Finder
08-29-2019
03:01 AM
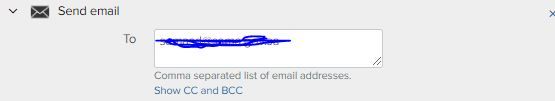
under correlation search can we add certain variables like $src$ | $dest$ into search name:
actually we are sending these notables to ticketing system through email. the in between machanism automatically opens the ticket for SOC if the email sent to certain email id.
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
starcher
Influencer
08-29-2019
05:53 AM
No. That is what the rule_title is for. Then combine the expand token command. Or construct your own field in the correlation search.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
starcher
Influencer
08-29-2019
05:53 AM
No. That is what the rule_title is for. Then combine the expand token command. Or construct your own field in the correlation search.
Get Updates on the Splunk Community!
Building Reliable Asset and Identity Frameworks in Splunk ES
Accurate asset and identity resolution is the backbone of security operations. Without it, alerts are ...
Cloud Monitoring Console - Unlocking Greater Visibility in SVC Usage Reporting
For Splunk Cloud customers, understanding and optimizing Splunk Virtual Compute (SVC) usage and resource ...
Automatic Discovery Part 3: Practical Use Cases
If you’ve enabled Automatic Discovery in your install of the Splunk Distribution of the OpenTelemetry ...