Join the Conversation
- Find Answers
- :
- Splunk Products
- :
- Splunk Enterprise Security
- :
- Trend Login Time Captures - Timechart Report for c...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
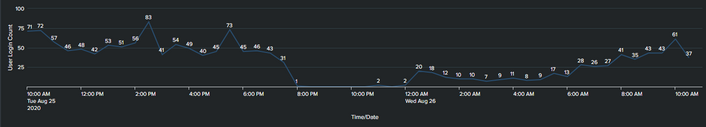
Trend Login Time Captures - Timechart Report for capturing the top logins times
Hi, I want to be able to visualise the top 1-5/10 login times based on a time range. So if I select a time range of 24 hours I'd like to be able to see the most frequent times users have logged in over an hour period. Not too fussed on the top listings but essentially I'd like this to display (based on the below) atop count.
Top Most Frequent Logins over an hour (24hr range)
1. Date 25/08/2020 10:00am -11:00am = 200
In theory, it would list only the highest login counts over an hr and then decent in count value from whatever top count I'd want.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am not sure what your base data is but let's assume it is a log of logins with timestamps. So, something like:
... base search ...
| bin _time span=1h
| stats count by _time
| sort -count
| where count >= 200
| head 5That is, bucket events into 1h bins, count events in those bins, sort counts descending, only take counts above 200, just take the top 5
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi this kind of works... but I am getting thousands of events where it should be only restricted to cs_username. This is my base search:
index=iis_prod sourcetype=iis site=AWS cs_Referer=*Login* sc_status=200 OR 302 cs_username=* cs_User_Agent!=Varnish_Health_Probe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Think I need to define the Login into a column and then search the count based on that whereby _time and Logins >200 are. The results I am getting is all the time events