Join the Conversation
- Find Answers
- :
- Premium Solutions
- :
- Splunk Enterprise Security
- :
- Splunk Enterprise Security: How to view events ass...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
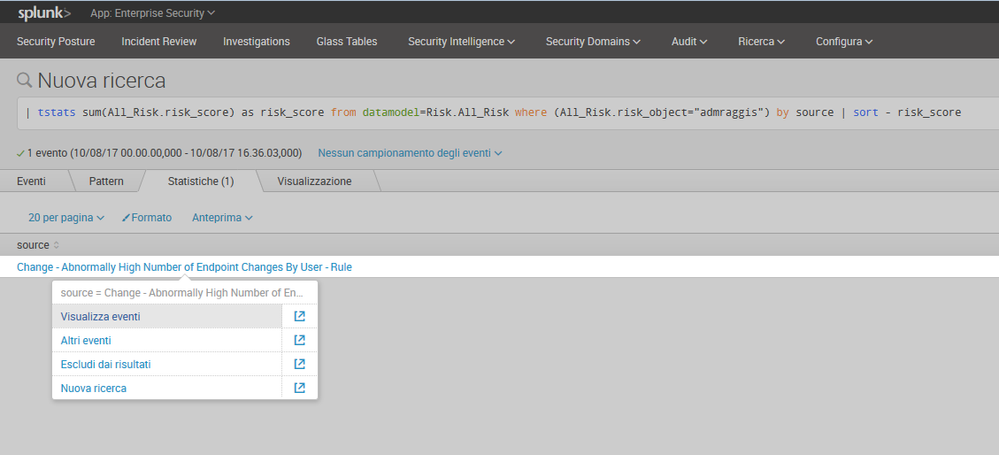
Splunk Enterprise Security: How to view events associated to "Change - Abnormally High Number of Endpoint Changes by User - Rule" source?
Hello,
i would like to see the Events associated to this source "Change - Abnormally High Number of Endpoint Changes by User - Rule" How can i view them?
When i click on "Visualize Event" nothing happen.
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Apologies to update an old thread but as I was looking into tuning this alert myself I thought I'd take the time to give an answer for the 2k views still wondering:
Take a look at the alerts search string itself, it's using "datamodel=Change_Analysis.All_Changes", so the "All_Changes" dataset of the "Change_Analysis" datamodel. You can view events from this by using either:
| datamodel Change_Analysis All_Changes search
or
| from datamodel:Change_Analysis.All_Changes
I ended up tuning out the audittrail and fs_notification sourcetypes from the datamodel as they were generating noise and not needed in my use case.
You can then of course add fields to the datamodel where needed, and include them in the alert search with something along the lines of
| tstats summariesonly=false allow_old_summaries=true count as change_count values(All_Changes.src) as "Source" values(All_Changes.Operation) as "Operation" values(All_Changes.dest) as "Destination" from datamodel=Change_Analysis.All_Changes...etc
and lastly (and optionally) tack on a | fields - WhereCIX to the end of the search to make the alert a bit more readable.
Hopefully that helps those still wondering