Are you a member of the Splunk Community?
- Find Answers
- :
- Premium Solutions
- :
- Splunk Enterprise Security
- :
- How to use a heavy forwarder to collect asset and ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to use a heavy forwarder to collect asset and identity information for Splunk Enterprise Security on Splunk Cloud?
HI!
I'm following the following directions to try and set up assets and identities for Splunk Enterprise Security on Splunk Cloud through a heavy forwarder.
https://www.hurricanelabs.com/blog/gathering-ldap-identity-data-with-splunk-cloud
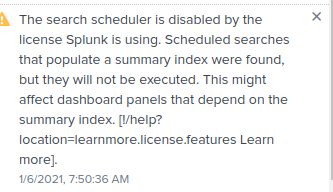
The instructions say to set up a saved search on the Heavy Forwarder and have it populate a summary index. However, I am unable to schedule searches on the Heavy Forwarder and get the message:
The search scheduler is disabled by
the license Splunk is using. Scheduled
searches that populate a summary index
were found, but they will not be
executed. This might affect dashboard
panels that depend on the summary
index.
[!/help?location=learnmore.license.features
Learn more]
Does anyone have any tips on what I am missing?
Thanks,
JG
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi I am using free trial of splunk I am dealing with this problem too with universal or heavy forwarder and I can't even open a ticket.
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Open a ticket with Support, and explain what you are trying to do. They will get you a 1mb license that enables the deployment server and other enterprise features. (These are available for 30 days after installing, but then rolls to limited license.)