Are you a member of the Splunk Community?
- Find Answers
- :
- Splunk Administration
- :
- Admin Other
- :
- Security
- :
- Creating a custom SOC monitoring dashboard using t...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
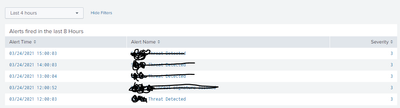
Creating a custom SOC monitoring dashboard using triggered alerts
index=_audit action=alert_fired ss_app="Threats_App"
| eval ttl=expiration-now()
| search ttl>0
| convert ctime(trigger_time)
| sort - trigger_time
| table trigger_time ss_name severity
| rename trigger_time as "Alert Time" ss_name as "Alert Name" severity as "Severity"
I created a dashboard, panel with above query in it. It is looking for triggered alerts from my app. I want to display the results(stats) of the triggered alerts in a different panel below that in the same dashboard.
so its like " here are the alerts fired and when u click the alert name, it shows the stats(results) of that alert. Implementing this , I can see multiple alerts and the results of those alerts in the same dashboard"
I do not want to install additional apps, so please help me with this query only. Please do not suggest apps for a simple solution. Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have this panel which keeps updating with new alerts(query posted in my earlier post). When I click on the alert, it should show me events on the same dashboard.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @aferns0804 ,
I understand 50% of your question, but I did not get what you are referring the result(stats) of the alert means?
To implement the concept, you can use the drildown option for the respective panel to populate the token value and create a another panel which will use this token as input in the query.