Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Windows IIS logs not formatting correctly / hostna...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Windows IIS logs not formatting correctly / hostname problem
So bringing in some IIS logs from a few windows servers... seemed pretty simple. Installed the add-on for Micrsoft IIS which gave me a few new sourcetypes to use.
My inputs.conf reads (star.log is actually *.log):
[monitor://C:\inetpub\logs\LogFiles\W3SVC1\star.log]
index = iis
sourcetype = ms:iis:default
disabled = false
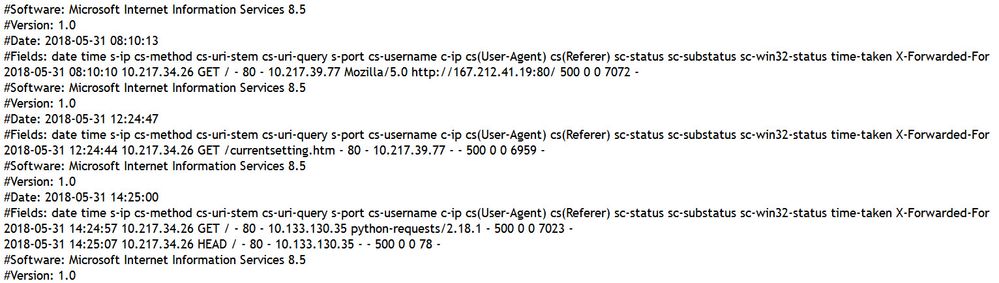
Event break are all chopped up. I looked at the source data from the IIS server and it looks like this (see image)
I also noticed that the hostname is coming in as "cs-method" and not the actual hostname. This server is sending in other logs from the splunk forwarder just fine, with the correct hostname.
Any pointers? Struggling here.
Thanks!
Joe
Splunk Enterprise v6.5.0
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am also having issues with the host field appearing when i run a search for this data. I commented out the field alias in props and for some reason the host field still does not exist in the search. When running a tstats on the index by host we see values for host. But not when we just simply search the data
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Your inputs.conf settings are fine. You'll want to take a look at the ./Splunk_TA_microsoft-iis/default/props.conf file on your search head. There's a bunch of over-ambitious FIELDALIAS commands there, and depending on exactly what fields you're logging from IIS, those FIELDALIAS commands can jack-up your field extractions.
I recommend commenting out this one:
FIELDALIAS-s_computername = s_computername as host
And either do a debug/refresh on your search head, or just restart the search head if that won't bum people out.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I just went to the app in manage apps, viewed the objects, found the aforementioned field alias and unchecked the "Overwrite field values" box - on my search head. Now I see the right host names associated with the events.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Once you've figured out which FIELDALIAS commands are the problem, you can actually override them in a ./Splunk_TA_microsoft-iis/local/props.conf file by setting them equal to nothing, like:
FIELDALIAS-s_computername =
That's a better practice than making changes to the stuff in ./default.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content