Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Why are all events being filter except for EventCo...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi
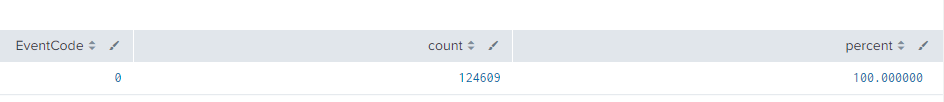
I'm filtering windows events from the Heavy Forwarder, everything works fine, all events are filtered except for EventCode = 0 any idea why?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
EventCode 0 was not being filtered because it is an Application event and not a security event.
In this way I solved it
props.conf
[source::WinEventLog:Application]
TRANSFORMS-wmi = setnull2
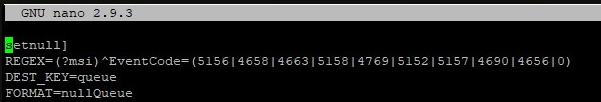
transforms.conf
[setnull2]
REGEX= (?msi) ^EventCode=(0)
DEST_KEY=queue
FORMAT=nullQueue
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
EventCode 0 was not being filtered because it is an Application event and not a security event.
In this way I solved it
props.conf
[source::WinEventLog:Application]
TRANSFORMS-wmi = setnull2
transforms.conf
[setnull2]
REGEX= (?msi) ^EventCode=(0)
DEST_KEY=queue
FORMAT=nullQueue
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We were able to filter it out from the UF using the following in our inputs.conf:
[WinEventLog://Application]
disabled = 0
index = windows_index
blacklist1 = EventCode="0"