Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Re: WatchGuard FireBox Assistance
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
WatchGuard FireBox Assistance
Hello Everyone,
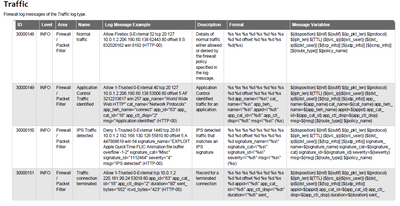
I'm hoping to get some assistance. My company using WatchGuard Firebox firewalls. I'm working to get the data correcting ingested into Splunk and get all the fields extracted (HIGHLY prefer a CIM complaint format) but the only WatchGuard App and TA Addon I've found are outdated, poorly written (I've been told) and are not CIM compliant. Is there an easy way to pull the information from the WatchGuard Log Catalog (https://www.watchguard.com/help/docs/fireware/12/en-US/log_catalog/Log-Catalog_v12_5.pdf) and put it into Splunk to properly ingest and label the data coming in from WatchGuard logs?
Thanks for any and all assistance with this!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @AJSCSA ,
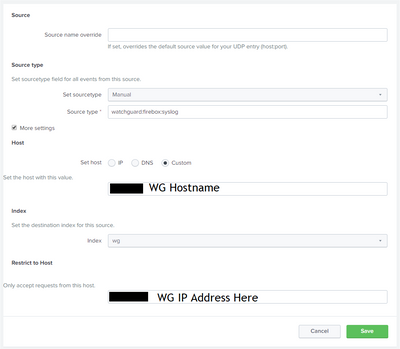
Do you have properly configured soucretype ?
Also I have got one doc please try that out.
https://www.watchguard.com/help/docs/help-center/en-US/Content/Integration-Guides/General/splunk_int...
--------------------------------------------------------------------------
If this helps your like will be appreciate. 😊
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi there,
First of all, I am not a professional splunker but due to my case, I have to dig deep for some scenarios on the watchguard firebox devices.
Please note that, based on my experience so far on watchguard (again I am not guru) the app and add-on does not handle the fields extraction properly.
I just used them so far for the source type (watchguard:firebox:syslog) and I am extracting most of the fields on my own.
Please advise which fields do you need them the most, maybe we can help each other.
I am using this regular expression for for Source_IP, Destination_IP, Source_Port and Destination_Port:
(?<src_ip>\d+\.\d+\.\d+\.\d+) (?<dst_ip>\d+\.\d+\.\d+\.\d+) (?<src_portt>\d+) (?<dst_port>\d+)
So far it covers all my needs for the required searches/dashboards.
(do not forget the SPACES)
Please advise if it helps you.
Regards,
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Any chance anyone could look at this and offer some advice? Thanks!