Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Partial obfuscation in Splunk Cloud
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Partial obfuscation in Splunk Cloud
Hello experts,
I'm trying to obfuscate the UserName and ComputerName from my events before indexation, while keeping the possibility of using the data to group from a common source.
Configuration: data are pushed by a UniversalForwarder (no transform options) to a SplunkCloud instance (limited setup).
Example:
I have this:
time1|UserName=user1|ComputerName=FR1234|EventStart
time2|UserName=user1|ComputerName=FR1234|EventEnd
time3|UserName=user2|ComputerName=US4321|EventStart
time4|UserName=user2|ComputerName=US4321|EventEnd
time5|UserName=user1|ComputerName=US4321|EventStart
time6|UserName=user1|ComputerName=US4321|EventEnd
And want something like this:
time1|UserName=#####|ComputerName=FR#|GeneratedSessionID=eifiweuh|EventStart
time2|UserName=#####|ComputerName=FR#|GeneratedSessionID=eifiweuh|EventEnd
time3|UserName=#####|ComputerName=US#|GeneratedSessionID=fwefwe|EventStart
time4|UserName=#####|ComputerName=US#|GeneratedSessionID=fwefwe|EventEnd
time5|UserName=#####|ComputerName=US#|GeneratedSessionID=hkukuyy|EventStart
time6|UserName=#####|ComputerName=US#|GeneratedSessionID=hkukuyy|EventEnd
Where GeneratedSessionID=function(user1,FR1234,encryptKey) or something similar. Meaning that the same couple computer+user will always create the same GeneratedSessionID
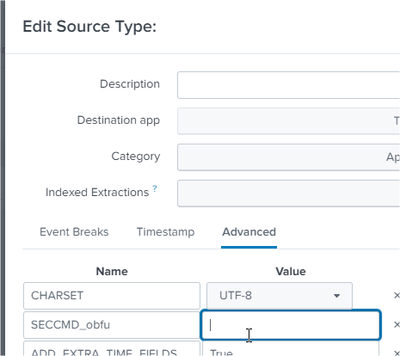
I'm looking at adding a SECCMD setting on the Advanced tab of my SourceType. I see how to anonymize the UserName and ComputerName, but not how to add a new field based on the others.
Any advise in that direction would be welcome, or any solution that will match with the restriction of my configuration.
Thanks in advance
Florent