Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- How to make sure files containing a particular pai...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to make sure files containing a particular pair of letters are properly blacklisted?
This is what I have started:
[monitor:///web/apps/doms/domains/*/CrewAdminAdapter.log]
index=wlsseappslogs
blacklist = *gc*\.log$
sourcetype = CrewAdminAdapter
crcSalt=
There are logs that look like: cw_nms_msa_ms011_gc060.log I don't want any of the logs that look like this but there are other logs very similar to this that I do want but they don't contain _gc which is our garbage collection file.
How do I keep those files from coming in with my blacklisting?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
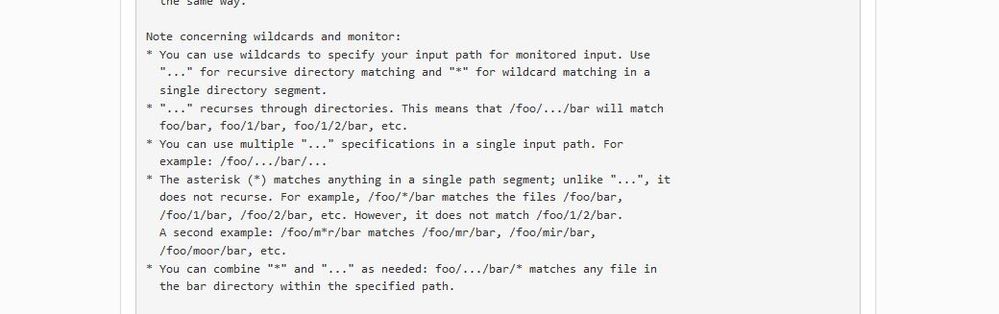
As we just spoke about in the other thread at Is it possible to use regular expressions and wildcard in the monitoring stanza of inputs.conf?
Says -
The syntax is of wildcard and not regex. So, blacklist = *gc*.log should work and not blacklist = *gc*\.log$
You should be abe to validate it using ls *gc*.log.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
ddrillic,
The use of regular expressions within a blacklist is allowed.
The use of regular expressions within [monitor://....] is not allowed.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
sorry the line is gc.log$