Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- How to extract JSON fields with transforms.conf fr...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to extract JSON fields with transforms.conf from UI?
Hi,
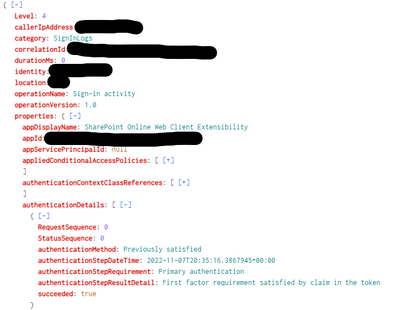
I need to extract several fields from my JSON logs. For example I have a login event like this:
I need to create e field "action" when category=SignInLogs and succeeded (last field) is equal to true or false generating the field action=success or action=failure to be CIM compliant. This value is already extracted under the field "properties.authenticationDetails{}.succeeded. Is it possible to do that by fields transformation in Splunk UI?
Thanks in advance!!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In Fields->Calculated fields make a calculated field called action and associate it with the sourcetype. The definition would be
if(category="SignInLogs", if('properties.authenticationDetails{}.succeeded'="true", "success", "failure"), action)A double if, so if category is not SignInLogs, it will just use any existing action value
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @bowesmana ,
it seems working fine, but this field properties.authenticationDetails{}.succeeded is not always present within the logs, so in this case I will have action=failure even if the field is not present. Is there a solution to populate the field action only when the field properties.authenticationDetails{}.succeeded is present?
Thank you in advance!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just add in another "if" clause
if(category="SignInLogs", if('properties.authenticationDetails{}.succeeded'="true", "success", if(isnotnull('properties.authenticationDetails{}.succeeded'), "failure", action)), action)Gets a bit messy with 3 levels of if, you could do it with a 'case' statement, but it would probably be longer anyway