Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Getting UDP data
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Getting UDP data
Hi,
This is default standalone setup. I'm trying to get data in from a network device which sends data as syslog on UDP/5114.
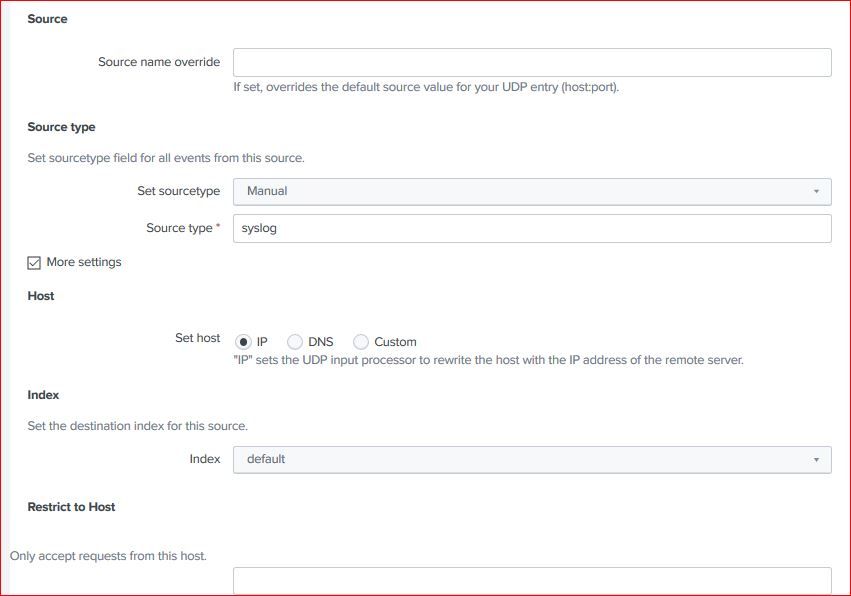
I've configured the UDP/5114 on Splunk. Here are the screenshots of config.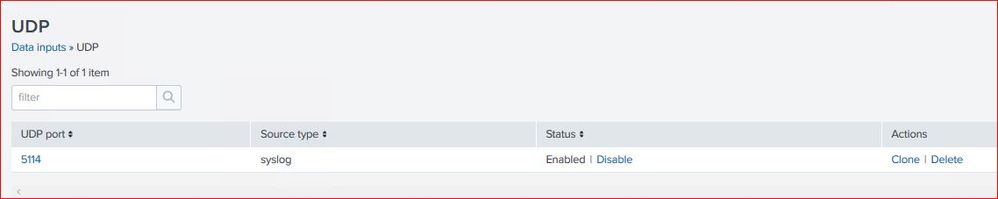
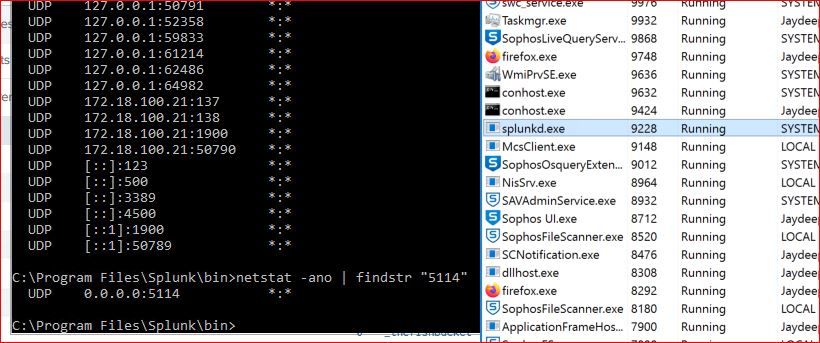
I've confirmed that splunk process is listening on port 5114
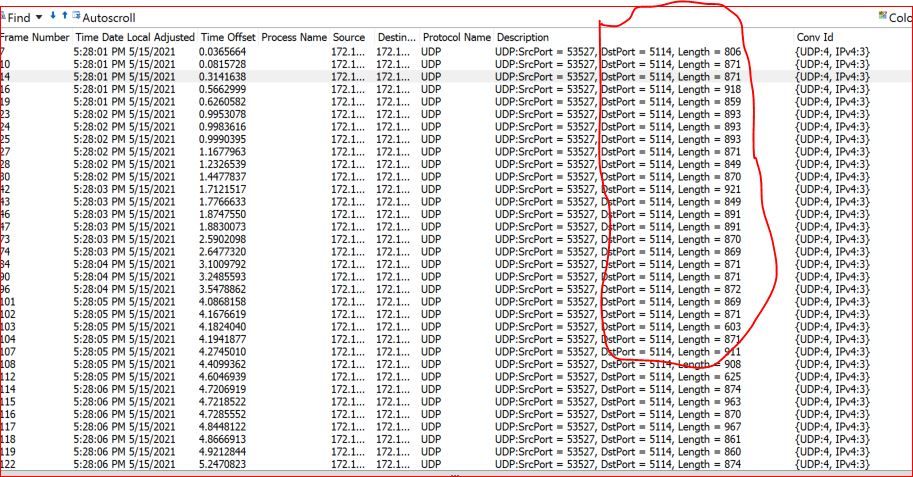
I've also confirmed that I'm getting data on host so no network routing or firewall issue. Bellow is a screenshot of MS Network monitor showing data received on port UDP/5114.
Yet no data is coming in the splunk instance.
Pls help resolve this.
--
Thanks & Regards.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm not sure about MS Network Monitor (now deprecated btw) - never used it - but Wireshark, for example, just dumps packets from the network interface. Which doesn't mean that they don't get filtered on a host firewall afterwards.
Since you're using UDP which is stateless, connectionless and so on, unless you're actively denying the packets (sending ICMPs), there will be nothing on the network informing you whether the recipient received the packets correctly or not.
So I'd search the firewall rules again.
And two more remarks:
1) If possible, use TCP - it's much more reliable and less prone to event loss
2) Splunk's syslog inputs don't scale well so if you're planning on having big volumes of data ingested this way, consider other forms of providing the source data to Splunk - there are a few methods that can be used (for example - a syslog server writing to buffer file and UF reading that file or a syslog server receiving the events and pushing them to HEC input via HTTP).
But to have something to begin with Splunk's syslog inputs are OK.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Everyone,
Can anyone pls help on this.?
--
Thanks & Regards
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you considered using Splunk Connect for Syslog (SC4S)?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Considering now. Any comment on the mentioned config.? Is there anything I'm missing in config.? Or any other troubleshooting pointers.?
--
Thanks & Regards.
