Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- GeneratingCommand intended behaviour?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
GeneratingCommand intended behaviour?
I've been writing custom commands using SCP1, particularly using splunk.Intersplunk.outputStreamResults and it's been great to use. To give some context, the command hits an API that exposes JSON which ultimately ends up in Splunk. However, I've been wanting to make use of SCP2's GeneratingCommand class to take advantage of getting the earliest & latest start times from a Splunk search.
I've been testing SCP2 and the GeneratingCommand class but am noticing some strange behaviour, especially when viewing the events in Splunk. This might be intended, but I just wanted to see if anyone else has come across similar and perhaps point me in the correct direction ?
I'm using:
- python-sdk-1.6.4
- Splunk 6.6.3
Example:
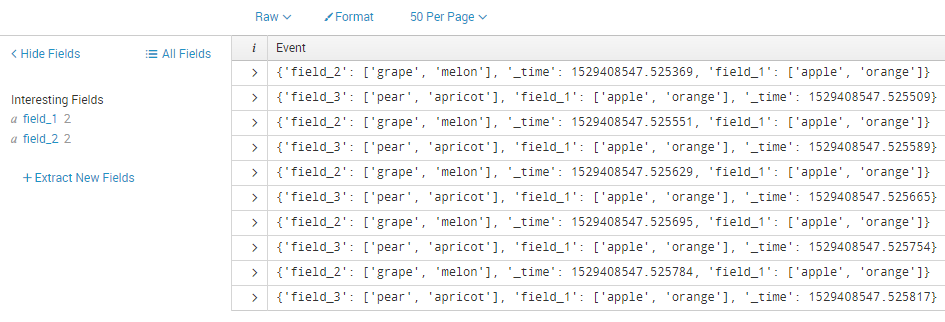
for x in range(10):
row = {}
row['field_1'] = ['apple', 'orange']
if x % 2 == 0:
row['field_2'] = ['grape', 'melon']
else:
row['field_3'] = ['pear', 'apricot']
row['_time'] = time.time()
row['_raw'] = str(row)
yield row
So my question is, why is field_3 missing?
If I make the following changes to the snippet, then all 3 fields are extracted by Splunk.
for x in range(10):
row = {}
row['field_1'] = ['apple', 'orange']
if x % 2 == 0:
row['field_2'] = ['grape', 'melon']
row['field_3'] = ['']
else:
row['field_3'] = ['pear', 'apricot']
row['field_2'] = ['']
row['_time'] = time.time()
row['_raw'] = str(row)
yield row
Any help or pointers would be most appreciated!