- Splunk Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Field extraction
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Splunkers!
I need to extract the specific field which dosent consists of sourcetype in logs,
Fields to extract - OS, OSRelease
Thanks in Advance,
Manoj Kumar S
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @smanojkumar,
in this case, please try this:
| rex "OS\=\"*(?<OS>[^,\"]*).*OSRelease\=\"*(?<OSRelease>[^,\"]*)"that you can test at https://regex101.com/r/SQFX88/1
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @smanojkumar ,
if you have the pair fieldname=fieldvalue, you should already have the extraction.
anyway, you could use two regexes like the following:
| rex "OS\=\"(?<OS>[^\"]*)"
| rex "OSRelease\=\"(?<OSRelease>[^\"]*)"Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @gcusello ,
Thanks for your response!
At rare cased we don't have " " in OS and OSRelease, What would be the regex, that should extract in both the cases, Like
OS="Windows", OS=Windows, OSRelease="jhvdhjc", OSRelease=nsvcv
Thanks in advance!
Manoj Kumar S
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @smanojkumar,
if you don't have quotes, you should be sue about the log forma to find a different rule, could you share some samples of your logs with and without quotes?
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
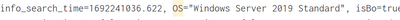
Without ""
info_search_time=1693969036.181, OS=Linux, isBo=false, isFo=false, SCOPE=Unknown, isVIP=false, OSType=Linux, isCACP=false, isCMDB=false, isLost=false, Country=Unknown, isIndus=false, isMcAfee=true, isStolen=false, OSRelease=Unknown,
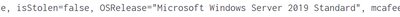
With ""
info_search_time=1693969036.181, OS="Windows Server 2019 Standard", isBo=true, isFo=false, SCOPE="IN", isVIP=false, OSType=Win, isCACP=false, isCMDB=true, isLost=false, Country=Germany, isIndus=false, isMcAfee=true, isStolen=false, OSRelease="EL Server 7.4 (Maipo", mcafee_LastCommunication="2023-09-05 20:30:35",
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @smanojkumar,
in this case, please try this:
| rex "OS\=\"*(?<OS>[^,\"]*).*OSRelease\=\"*(?<OSRelease>[^,\"]*)"that you can test at https://regex101.com/r/SQFX88/1
Ciao.
Giuseppe