Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Getting Data In
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Azure Authentication Logs - Authentication Method ...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Azure Authentication Logs - Authentication Method Field- How to filter?
Dmikos1271
Explorer
05-20-2022
08:03 AM
In our Splunk environment, we currently ingest Azure AD logs and we have three different sourcetypes:
azure:aad:signin
azure:aad:audit
azure:aad:user
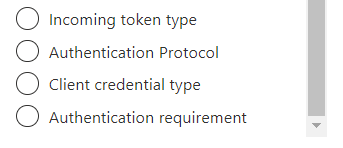
There no missing events and the ingested data is very rich. However, I don't see any way within the Splunk ingested Azure signin data to to filter by authentication method (Single-factor vs multi-factor). This is something that can be done via Azure Active Directory, Monitoring, Sign-in logs but I do not see any reference to it in my Splunk data (I do see a lot of conditional access enforcement and the other primary fields, but not any of the secondary fields that could be used for filtering in Azure):
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
dansyring
New Member
10-21-2025
10:14 AM
Did you find an answer to this?
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
Mile High Learning with Splunk University, Denver, Colorado
If Denver is known for its mile-high elevation, Splunk University is about to raise the bar on technical ...
IT Service Intelligence 5.0 Series: Your Guide to the June Launch
We are excited to announce the June release of Splunk IT Service Intelligence (ITSI) 5.0. This update ...
Agent Mode Engaged! Enchaining Agentic Operations with Splunk AI Assistant 2.0
Are you ready to transform how your team handles complex data requests?
We invite you to our upcoming ...