Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Dashboards & Visualizations
- :
- Alert UP and Down By Status Code
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Alert UP and Down By Status Code
Hi Splunk,
Newbie here 😅 want to ask about alert.
for example we have data like
| Name | Time | StatusCode |
| AAA | 2021-02-02 08:00 | 404 |
| AAA | 2021-02-02 08:01 | 200 |
| BBB | 2021-02-02 09:00 | 503 |
| CCC | 2021-02-02 09:01 | 404 |
| BBB | 2021-02-02 09:30 | 200 |
| CCC | 2021-02-02 09:30 | 200 |
How to create a alert base on table with cron every per 5 minutes. if StatusCode != 200 alert notif startdown and if StatusCode =200 alert notif Solved.
Example for the alert base on table:
"Hi AAA, you are down on 2021-02-02 08:00"
and email again if the AAA StatusCode changed to 200
"Hi AAA, you are now SOLVED on 2021-02-02 08:01"
done, until the StatusCode Changed to !=200 the alert send me the email again.
Another Example:
"Hi BBB, you are down on 2021-02-02 09:00"
then the StatusCode Changed to 200
"Hi BBB, you are now SOLVED on 2021-02-02 09:30"
On the splunk alert menu, we didn't find for reset alert when trigger condition is no longer true. So we need a help and advice.
Thank you
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hi @bernanda ,
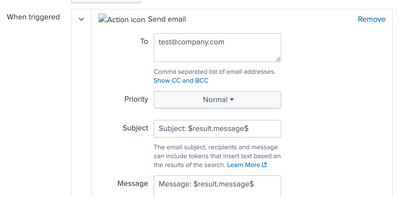
You can create a new field in your search and use it in the email subject/body.
<your_base_search> | eval message=if(Status_Code==200, "Hi ".Name.", you are now SOLVED on ".Time, "Hi ".Name.", you are down on ".Time)
You can use $result.message$ in the email subject/message body.
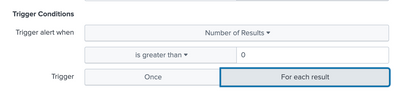
Change Trigger condition to trigger alert action per result.
If this reply helps you, an upvote/like would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi manjunathmeti
Thank you for your reply.
When I tried like your way, I got many alerts for the all Status with the correct message. That is funny to empty my inbox. but it's OK 😂
I think that is need a little conditions, just like a monitoring Uptime. If node get DOWN status then send me the a alert once. and then if the node get UP status send me the alert just once. But I still try to hard.
so, thanks for you