Are you a member of the Splunk Community?
- Find Answers
- :
- Apps & Add-ons
- :
- All Apps and Add-ons
- :
- how to replay the events in an index other than in...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I had uploaded the eventgen app on my splunk and used the following eventgen.conf file in $splunkHome/etc/apps/eventgen/local/eventgen.conf (which I found in the eventgen app website). I could see the events generated from eventgen app in the "main" index. But what changes do I have to make if I want to see the events in some other index other than the main index
[sample_tutorial 1.sample]
mode = replay
sampletype = csv
timeMultiple = 2
backfill = -15m
backfillSearch = index=main sourcetype=splunkd
outputMode = stdout
outputMode = splunkstream
splunkHost = localhost
splunkUser = admin
splunkPass = changeme
outputMode = file
fileName = /tmp/internal.log
token.0.token = \d{4}-\d{2}-\d{2} \d{2}:\d{2}:\d{2},\d{3,6}
token.0.replacementType = timestamp
token.0.replacement = %Y-%m-%d %H:%M:%S,%f
token.1.token = \d{2}-\d{2}-\d{4} \d{2}:\d{2}:\d{2}.\d{3,6}
token.1.replacementType = timestamp
token.1.replacement = %m-%d-%Y %H:%M:%S.%f
token.2.token = \d{2}/\w{3}/\d{4}:\d{2}:\d{2}:\d{2}.\d{3,6}
token.2.replacementType = timestamp
token.2.replacement = %d/%b/%Y:%H:%M:%S.%f
token.3.token = \d{4}-\d{2}-\d{2} \d{2}:\d{2}:\d{2}
token.3.replacementType = timestamp
token.3.replacement = %Y-%m-%d %H:%M:%S
token.4.token = \d{4}-\d{2}-\d{2}T\d{2}:\d{2}:\d{2}
token.4.replacementType = timestamp
token.4.replacement = %Y-%m-%dT%H:%M:%S
Sorry if make u little confused by my unformatted English language.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It should probably be something like -
[sample_tutorial 1.sample]
mode = replay
sampletype = csv
timeMultiple = 2
#backfill = -15m
#backfillSearch = index=main sourcetype=splunkd
index=<your index name>
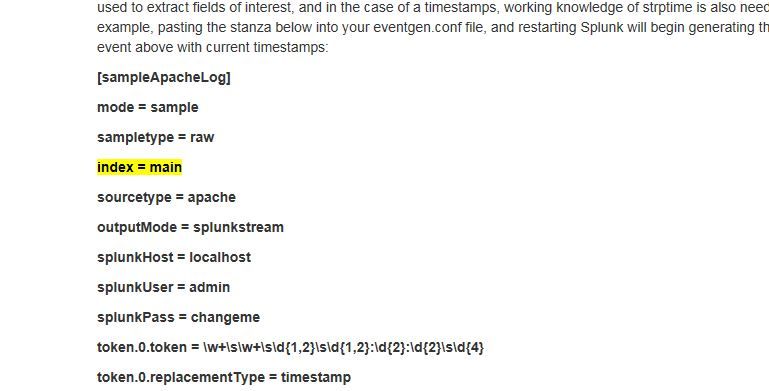
We can see a sample config at Simulating Data with the Splunk Event Generator
It shows -
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It should probably be something like -
[sample_tutorial 1.sample]
mode = replay
sampletype = csv
timeMultiple = 2
#backfill = -15m
#backfillSearch = index=main sourcetype=splunkd
index=<your index name>
We can see a sample config at Simulating Data with the Splunk Event Generator
It shows -