Join the Conversation
- Find Answers
- :
- Apps & Add-ons
- :
- All Apps and Add-ons
- :
- Re: Not getting results in several security dashbo...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Not getting results in several security dashboards
I'm getting events now, but for example I've looked at the "User Logon Failures" page. It doesn't return any results in any of the sections. I haven't looked at all of them, but the first one over time seems strange to me or maybe my data is strange.
It uses this:
search eventtype=msad-failed-user-logons
so I checked that eventtype and it's based on:
eventtype=msad-nt5-failed-user-logons OR eventtype=msad-nt6-failed-user-logons
I've got only 2008 R2 so I looked at the nt6 eventtype:
eventtype=wineventlog-security EventCode=4625 user!="*$"
This doesn't produce any search results for me as is. I removed the "user" field and get plenty of results. I can't actually see any "user" fields in the data I get.. however I have a field called "Account_Name" which seems to have the information I'm looking for. So I tried this search:
eventtype=wineventlog-security EventCode=4625 Account_Name!="*$"
I seem to get the failed logon attempts that the page is trying to retrieve. So I guess my question is.. is it normal for this to not work or should I actually have a "user" field?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
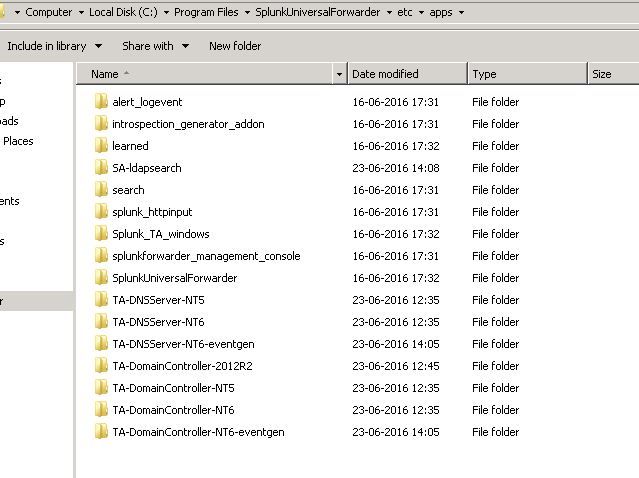
You need to add the splunk_TA_Windows to your splunk instance for field extractions. You can disable all the inputs in the app (and you should on a Linux box), or even just remove the inputs.conf file - we just need the field extractions.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am facing the same problem. I have put all the necessary add-on on the splunk forwarder , and installed on the indexer as well. I am not able to get the account name instead i am getting user field.
Please help
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ok so I read the instructions and I guess I misunderstood them. I thought that the AD app needed to be added to the index instance and the Windows_TA only to the DCs. But I added the Windows_TA to the splunk indexer and it seems to have fixed it. Even though I get a nasty error when opening the Windows_TA app since I'm using a Linux server.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've looked at the Windows Security Operations Center app and it seems to join the "User Name" and "Account_Name" fields to produce results.