Join the Conversation
- Find Answers
- :
- Apps & Add-ons
- :
- All Apps and Add-ons
- :
- Am i missing something or Splunk fails to extracti...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Am i missing something or Splunk fails to extracting fields from _raw randomly?
Hello Splunk Ninjas...
I came across some peculiar behaviors recently and cannot get my head around it...My best guess is to fully leverage the power of all your combined brains into shedding some light...eventually?
Here's the deal:
I get an incremental feed from an Oracle db via dbx2 and it seems to be working flawlessly. _raw is subsequently made of all combined db rows and column which displays onscreen as comma separated value events. For each event, there is an AUTHOR which I've validated from the db.
[base search] | table _raw, AUTHOR
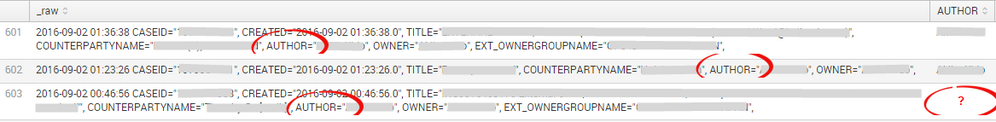
But, somewhat, the AUTHOR field failed to be extracted, even though is belongs to _raw as illustrated below:
Any clues ladies and gents?
Many thanks for your help.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Resolved with [base search] | eval AUTHOR=tostring(AUTHOR) | rex field=_raw "AUTHOR=\"(?<AUTHOR>\w+)\"" - Splunk devs - is this expected behaviour?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Actually scratch that out - this extract AUTHOR=Null...
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can try extracting field by field, something like -
| eval _raw="AUTHOR='name1'"
| rex field=_raw AUTHOR='(?<author_name>\w*)'
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am unsure of why the extraction for this field failed automatically, but you can certainly add a regular expression before your table expression to force splunk to do some additional field extraction.
something like
rex field=_raw "AUTHOR=\"(?<AUTHOR>\w+)"
So you would have
[base search] | [regex] | [stats or table..etc]
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
thank you bcatwork - this is what I've also try to apply as workaround but it doesn't force the extraction.Question remains though as why it ain't extracted automatically from some event, while it is from the others (99.8% of all events).