Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Alerting
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Other Using Splunk
- :
- Alerting
- :
- how can I do to create one search when I can see t...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
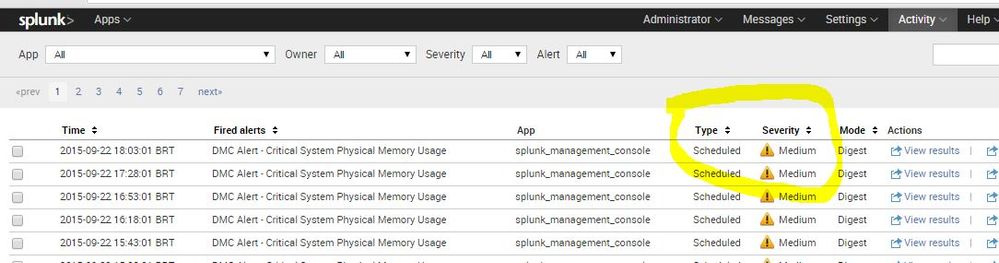
how can I do to create one search when I can see the severity of the alert?
samir_silva
New Member
09-22-2015
02:31 PM
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
gcato
Contributor
09-22-2015
05:19 PM
Hi Samir,
You can use the REST API to get this result. For example:
| rest /services/alerts/fired_alerts/-
|stats sum(triggered_alerts) AS count BY savedsearch_name, severity
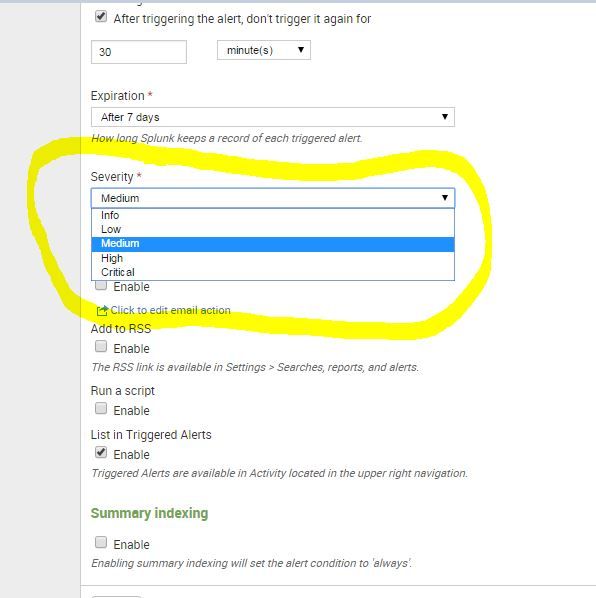
|eval severity = case(severity==1, "Info",
severity==2, "Low",
severity==3, "Medium",
severity==4, "High",
severity==5, "Critical")
|rename savedsearch_name AS Alert
|table Alert severity count
Hope this helps.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
samir_silva
New Member
09-24-2015
06:28 AM
Tranks for help,
My finish search.
| rest https://localhost:8089/servicesNS/your-user/-/alerts/fired_alerts/- |stats sum(triggered_alerts) AS count BY savedsearch_name, severity
|eval severity = case(severity==1, "Info",
severity==2, "Low",
severity==3, "Medium",
severity==4, "High",
severity==5, "Critical")
|rename savedsearch_name AS Alert
|table Alert severity count
|sort - count
Career Survey
First 500 qualified respondents will receive a $20 gift card! Tell us about your professional Splunk journey.
Get Updates on the Splunk Community!
Community Content Calendar, September edition
Welcome to another insightful post from our Community Content Calendar! We're thrilled to continue bringing ...
Splunkbase Unveils New App Listing Management Public Preview
Splunkbase Unveils New App Listing Management Public PreviewWe're thrilled to announce the public preview of ...
Leveraging Automated Threat Analysis Across the Splunk Ecosystem
Are you leveraging automation to its fullest potential in your threat detection strategy?Our upcoming Security ...