Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Other Using Splunk
- :
- Alerting
- :
- What is the difference between "Once" and "For eac...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What is the difference between "Once" and "For each result" in notable OR alert trigger conditions?
I know this has been already asked in the past, but it still not completely clear to me:
https://docs.splunk.com/Documentation/Splunk/latest/Alert/AlertTriggerConditions
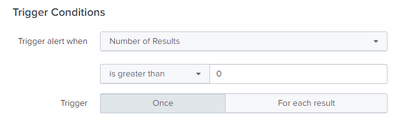
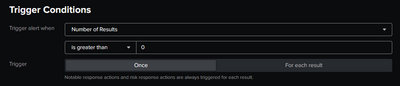
For testing purpose to understand the topic, I have set-up the following Correlation Search that triggers a Notable Event in Splunk Enterprise Security. The same can be done also as an Alert in Splunk Enterprise:
| makeresults count=3
| streamstats count | eval value=case(count=1,"test01",count=2,"test02",count=3,"test03") | eval alert=case(count=1,"KO",count=2,"OK",count=3,"KO")
| search alert="KO"
|`get_event_id`|eval orig_index=index|eval orig_indexer_guid=indexer_guid|eval orig_event_hash=event_hash|eval orig_cd=_cd|eval orig_raw=_raw
The above search run every 5 minutes and generates 2 events. I tried to change between "Once" and "For each result" but nothing change, they are always generated 2 Notable events.
I was expecting:
- "Once": generate only 1 Notable event
- "For each result": generate 2 Notable events
So the question is which is the difference between "Once" and "For each result" and why there is no effect changing it in my test?
Thanks a lot,
Edoardo
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
***Notable response actions and risk response actions are always triggered for each result.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
IF you search generate 2 results, in the "once" options , yo will receive one alert with 2 results, but if is "For each result", you will receive 2 alerts, one for each result
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The behavior that you are expecting is indeed supposed to be what happens. I have tested your search with a basic alert (not an ES correlation search) and with "once" it only triggers the log_event alert action when the alert runs. When switched to "for each result" it triggers it twice, for both results.
Are you sure that you do not have two versions of the same alert running?
Also, have you tried scheduling a normal alert (not a correlation search alert) and changing the alert_action to "Log Event" and see if the behavior is different? It could possibly be a bug with the notable event alert action.
Lastly, is this from within ES?