Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Other Using Splunk
- :
- Alerting
- :
- Alert help needed - Filtered events are still appe...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I only want my alert to trigger if a particular field value has failed 2 or more times in the last 50 occurances. My current search is:
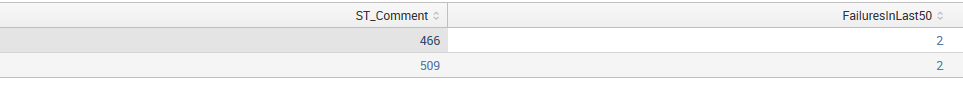
sourcetype=mySource ST_Script="myScript.py" ST_LogType="Step Log" | dedup 50 ST_Comment | search ST_Status=Fail | stats count AS FailuresInLast50 by ST_Comment | where FailuresInLast50 >= 2
From the statistics tab this search appears to do what I wanted because only fields with 2 or more failures are appearing:
However when I go to create my alert condition (FailuresInLast50 count >= 2) I get an error because it can't parse my alert condition. I assume I'm going about this in slightly the wrong way, so some guidance would be much appreciated.
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You are trying to do the same thresh-holding work twice: once in your search and once in your alert trigger. You need to pick one place or the other. So let's keep your search exactly as it is. In this case, you need your alert Trigger condition to be Number of Results is Greater than 0. If you think about it, you will see what I mean but if not, just trust me and configure it this way and it will work.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You are trying to do the same thresh-holding work twice: once in your search and once in your alert trigger. You need to pick one place or the other. So let's keep your search exactly as it is. In this case, you need your alert Trigger condition to be Number of Results is Greater than 0. If you think about it, you will see what I mean but if not, just trust me and configure it this way and it will work.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for your answer, I'll give it a go and report back!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
LOL. Sometimes that's how you have to explain it.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You asked all valued that are 2 or higher, therefore having events with where FailuresInLast50=2 is expected.
Are you sure tat all your values are not 2 ?
Can you run the same search without the "where" condition then see if you have values >2