Are you a member of the Splunk Community?
- Find Answers
- :
- Premium Solutions
- :
- Splunk Enterprise Security
- :
- Splunk Enterprise Security: How to ingest firewall...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Splunk Enterprise Security: How to ingest firewall ,waf ,ssandbox ,email gateway, endpoints logs to datamodels
How can I ingest firewall ,waf ,ssandbox ,email gateway, endpoints logs to Splunk ES datamodels?
I am trying to work on Splunk ES dashboards with the below details:
WAF Issues
Firewall Issues
Malware Reports
DLP Activities
DDAN
These are the sources to look for:
• network traffic : (firewall ip address) (proxy: ip address) (imsva (mail gatewa) ip address - shqimsva), ip address
• malware: ip address (apex central - index is trendmicro) proxy and mail gateway , ip address
• dlp: ip address (apex central - index trendmicro), mail gateway [DLP_Credit Card info] -
• waf = ip address
• web center (waf, iwsva proxy ip address)
Dashboards are not loading details about the above logs.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You are asking multiple questions at once that are very vague. It would be helpful to have a question with each specific source you are working with allowing those with experience in specific technologies to help you. For the portion of your sources that happen to be syslog based connections you may want to check out the new Splunk Connect for Syslog
https://splunk-connect-for-syslog.readthedocs.io/en/latest/sources/
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
thanks for the info but it seems
• Asset and Identity has not been configured that results in showing unknown values in many dashboards
• Data Mapping and Normalization has not been done properly
the above issues needs to be resolved first do you have any idea on this
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Because this is a new install I would suggest connecting with your SE who may recommend services time to assist in initial deployment.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dear Friend,
Thanks for the info, this is not a new implementation, we had ES 4.7 installled and now it is upgraded to 5.2.2, exisitng splunk enterprise is 7.2.1
We are having difficulties in data mapping and data normalisations.
Regards,
Rahul.K
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You need this app:
https://splunkbase.splunk.com/app/2968/
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
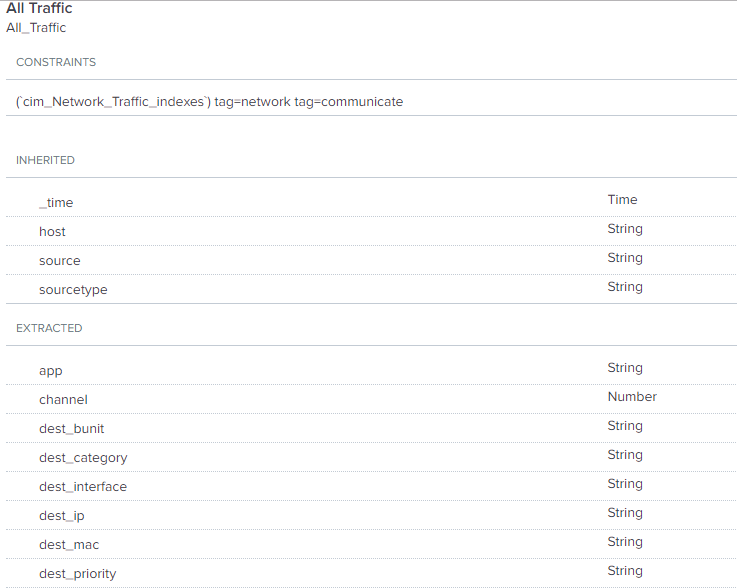
First you need to make sure your data is CIM (Common Information Model) compliant. This is to normalize the data so you are using the same field values for the datamodel. You will want to look at each data model for the Common names and then check your data that corresponds to that datamodel. https://docs.splunk.com/Documentation/CIM/4.13.0/User/Overview
Example for Network Datamodel: https://docs.splunk.com/Documentation/CIM/4.13.0/User/NetworkTraffic
The data also needs to be tagged properly. Network traffic has the tag of network and communication. This is typically done through the app but you will need to check this as well.
This is is where I would start and move through each datamodel and data source you are having issues with.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
where can we get all the indexes details about all datamodels in CIM
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the info but i tried malware dashbnoard with CIM malware index and tag =malware tag=attack....however it doesnot shows the malware detected by trendmicro deep discovery analyzer.
i have checked app as smtp , signature ,policy but no way i am tired of this datamodels even though mu dashboard like
intrusin center
malware
network resolution DNS
vulnearbilites
risk
threat
endpoint
DLP
dashboards are showing some data but i need to have real time datas from deep discovery analyszer , trendmicro apex central, firewalls , fortinet , trendmicro waf....
not sure what to do ....also because of ES now my indexer has also started crashing...
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you are having issues with the stability of your environment, I would open a Support case.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
can you give an example showing how do you map data in datamodels using your network devices as source.
for ex:source is trendmicro, data model is malware how can you configure the datamodel.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
When you search your trend micro data, does this data have a tag field? You will see this on the left hand side when searching your data as Selected fields or Interesting fields. If you are having issues with your Splunk server, I would recommend calling support and asking for assistance in making changes to your datamodels as this can impact the performance of your Splunk environment.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
how to make sureor check that your data is CIM (Common Information Model) compliant
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Search the data in question to make sure fields, for the datamodel they need to be a part, exist. Also check the for the field tag. The data needs to be tagged appropriately for that data model as well (tag=network and communicate). So your firewall data should follow the Network traffic data model. If the firewall has an IPS/IDS and that data is sent to Splunk, it will need to follow the datamodel Intrusion Detection field names and tags=ids and attack.