Are you a member of the Splunk Community?
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- What are the ports that I need to open?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
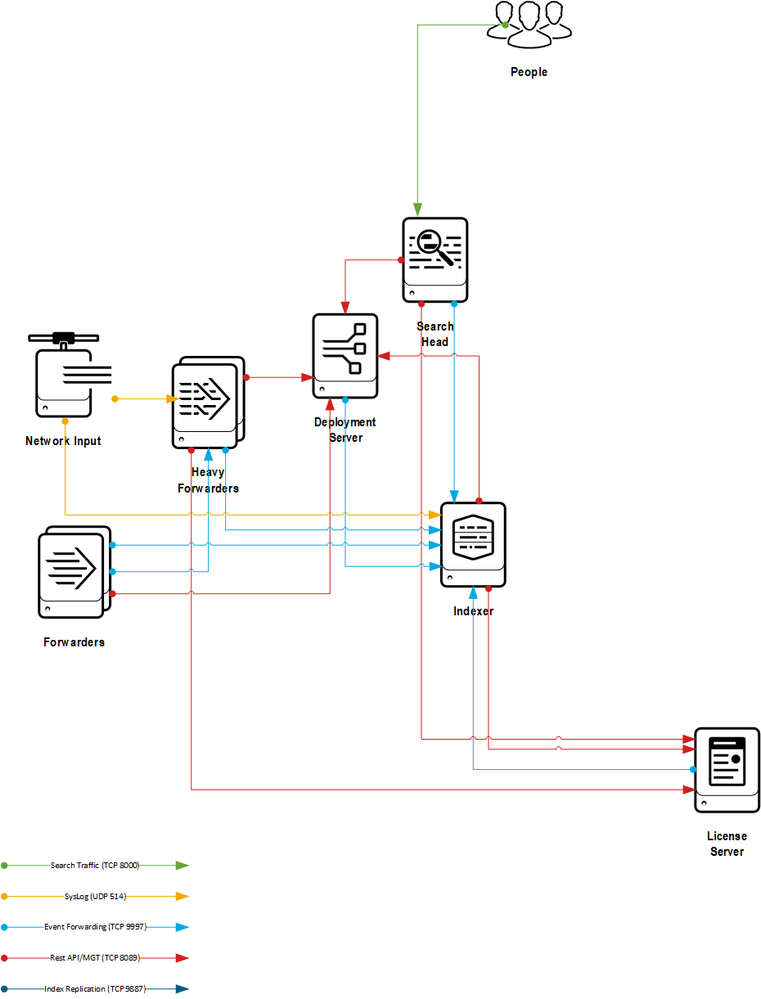
defaults are
9997 for forwarders to the Splunk indexer.
8000 for clients to the Splunk Search page
8089 for splunkd (also used by deployment server).
All of these can be changed if desired.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The Splunk Documentation has a page that discusses which ports need to be opened, and has diagrams for both standalone and distributed deployments:
Components and their relationship with the network - in the Inherited Deployments Manual
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
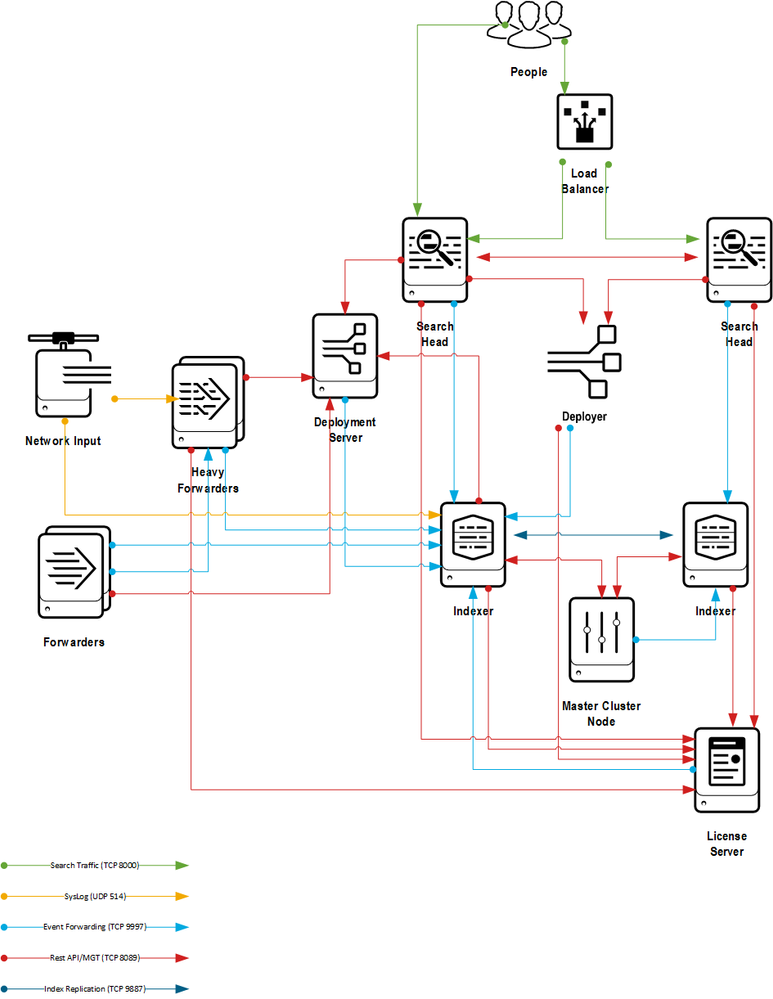
Nice use of colors. One change you may want to review is the direction on the deployer arrows. My understanding is that clients do a pull form a Deployment Server vs the Deployer initiating a push to search peers in a cluster.
Rob
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is there an updated version of this visio for clustered search heads and indexers?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Per request, source Visio diagrams are here:
http://downloads.jordan2000.com/splunk/
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've taken the liberty of updating the diagram slightly to reflect both changes in code since 6.2 and recommendations between this and one other post.
JPG format: https://drive.google.com/open?id=0B3PXaVtuNWbnMzJ6bTlkcXRmMFE
Visio format: https://drive.google.com/open?id=0B3PXaVtuNWbnRGtyM2phX2tWQ3M
Thanks @rob_jordan for the great effort and for sharing!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Also note that for Search Head Clustering there is a new replication port that you can pick, e.g. 8181. Also with SHC you need the KV store port (by default, 8191) must be available to all other members. You can use the CLI command splunk show kvstore-port to identify the port number.
The replication port must be available to all other members.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Since splunk 6.2 also port 8191 is used for the kvstore.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It seems many are confused about port required from UFs to a HF. Which is 9997 too i.e.
UFs ---9997---> HF --- 9997---> Indexers
UFs, Indexers, SHs ---8089 ---> DS
Many uses HF & DS as same server.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is a diagram of Splunk components and network ports that are commonly used in a Splunk Enterprise environment. Firewall rules often need to be updated to allow communication on ports 8000, 8089, 9997, 514 and others.
Source files available here: http://downloads.jordan2000.com/splunk/
Updated version

Original version

- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Many thanks for sharing. this is very useful, clear.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Little typo there on the MANAGEMENT TIER.
Does anybody have a version of this made specifically for opening firewall ports between an on-premise installation and splunkcloud.com?
Thanks!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can anybody me with the commands to specifically opening firewall ports foe an on-premise installation?
Also, what ports to open and how to open the ports?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is excellent. Very helpful.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I downvoted this post because for analysis
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Amazing, exactly what I needed
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We're working on getting this or something like this added to the main documentation. We'll keep you posted on where and when (soon!)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks,
I think https://docs.splunk.com/Documentation/Splunk/9.2.1/InheritedDeployment/Ports is the one included?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for this diagram, kind sir.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@rob_jordan : Your picture speaks 100000k words 🙂 very helpful