Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Dashboards & Visualizations
- :
- Dashboard drilldown of _raw log query not producin...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Splunk Community,
I'm setting up a new Dashboard view for one of our apps, and I'm having issues with the drilldown option. I cloned another view that works perfectly, which is for similar logs from our firewall (Forward Traffic). When you click on a specific item in the initial output, it is supposed to drilldown and give you the raw syslog from that specific event. However, it's not working for this new view. Below an example from the XML:
<title>Failed Logins</title>
<search>
<query>index=netfw logdesc="SSL VPN login fail" | table _raw _time devname user remip msg reason</query>
<earliest>$field1.earliest$</earliest>
<latest>$field1.latest$</latest>
<sampleRatio>1</sampleRatio>
</search>
<option name="count">10</option>
<option name="dataOverlayMode">none</option>
<option name="drilldown">row</option>
<option name="percentagesRow">false</option>
<option name="rowNumbers">true</option>
<option name="totalsRow">false</option>
<option name="wrap">true</option>
<fields>["_time","devname","user","remip","msg","reason"]</fields>
<drilldown>
<set token="rawlog">$row._raw$</set>
</drilldown>
</table>
</panel>
</row>
<row>
<panel>
<table>
<title>RAW View</title>
<search>
<query>index=netfw "$rawlog$"</query>
<earliest>$field1.earliest$</earliest>
<latest>$field1.latest$</latest>
</search>
<option name="drilldown">none</option>
</table>
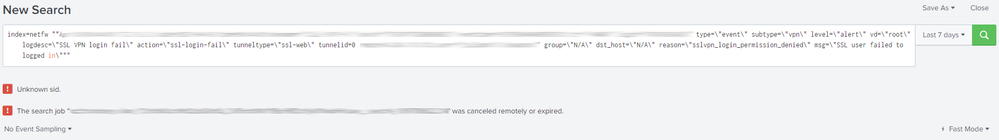
While the drilldown does not "work", when I check the results by clicking on the magnifying glass, it shows the proper output (index=netfw "raw log output from the clicked event"). However S&R shows 0 events.
What's odd is, if I copy and paste the raw log output inside of quotes in S&R, it will show 0 events. But, if I take the raw log from the other view that works and paste it in S&R inside of quotes, it pulls up that single event fine.
Another oddity, the problem logs that I can't cut and paste into search have the word "in" at the tail end of the log string, which is inside quotes. That "in", for "SSL user failed to logged in" is orange in the string.
Any help is much appreciated, I think that "in" could be the cause, but I'm new to splunk, SPL, etc. Below is the code from the working view, it's slightly different.
<row>
<panel>
<table>
<title>Forward Traffic Logs</title>
<search>
<query>index=netfw | table _raw _time devname srcip dstip action service policyid</query>
<earliest>$field1.earliest$</earliest>
<latest>$field1.latest$</latest>
<sampleRatio>1</sampleRatio>
</search>
<option name="count">10</option>
<option name="dataOverlayMode">none</option>
<option name="drilldown">row</option>
<option name="percentagesRow">false</option>
<option name="rowNumbers">true</option>
<option name="totalsRow">false</option>
<option name="wrap">true</option>
<fields>["_time","devname","srcip","dstip","action","service","policyid"]</fields>
<drilldown>
<set token="clientTok">$row._raw$</set>
<set token="forms.clientTok">$row._raw$</set>
<set token="resultrow">$row.srcip$</set>
<set token="forms.resultrow">$row.srcip$</set>
</drilldown>
</table>
</panel>
</row>
<row>
<panel>
<event>
<title>Complete Log Details</title>
<search>
<query>index=netfw "$clientTok$"</query>
<earliest>$field1.earliest$</earliest>
<latest>$field1.latest$</latest>
</search>
<option name="list.drilldown">none</option>
</event>
</panel>
</row>
<row>
<panel>
<table>
<title>RAW View</title>
<search>
<query>index=netfw "$clientTok$"</query>
<earliest>$field1.earliest$</earliest>
<latest>$field1.latest$</latest>
</search>
<option name="drilldown">none</option>
</table>
</panel>
</row>
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You need to escape the contents of the token
<query>index=netfw $clientTok|s$</query>- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You need to escape the contents of the token
<query>index=netfw $clientTok|s$</query>- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So, that did not work. The query you highlighted is actually the one that's working. The problem one is actually:
<query>index=netfw "$rawlog$"</query>
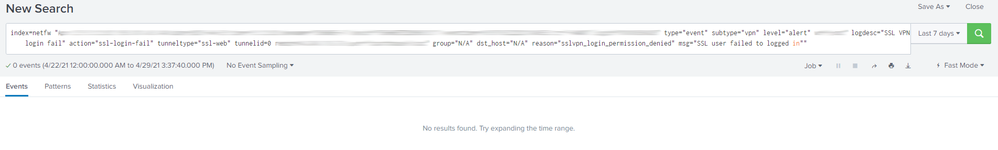
I tried what you noted, and it still did not work. The last "in" in the syslog string for that event is still highlighted and S&R shows no events that match.
ETA: Here is a screenshot, adding "|s" to the token actually added some errors:
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
As you can see from your screenshot, the value of the token is enclosed in double double-quotes. This is because you have put double quotes around the token. What I suggested was using the |s on the token without any double quotes around it (fair enough, I showed the example of the wrong token, but the principle is clear). The |s will put double quotes and it will escape other characters, including embedded double quotes as you can also see in your screenshot.
<query>index=netfw $rawlog|s$</query>
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That worked!!!
Thanks again, and I'm sorry I missed the quotes.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
My apologies, as I missed the quotes. I will try this and report back. I appreciate your help!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No one? Attached is a screenshot of the output from when you click on a log from the original query. As I said, it's working (so the XML is mostly good), however for some reason S&R isn't showing any results for the log, and that last "in" is highlighted orange like Splunk thinks it's SPL code.
Any help is appreciated.