Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Dev
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Apps & Add-ons
- :
- Splunk Development
- :
- Splunk Dev
- :
- Help with Event Search based on custom time field
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Help with Event Search based on custom time field
csahoo
Explorer
05-26-2022
05:55 AM
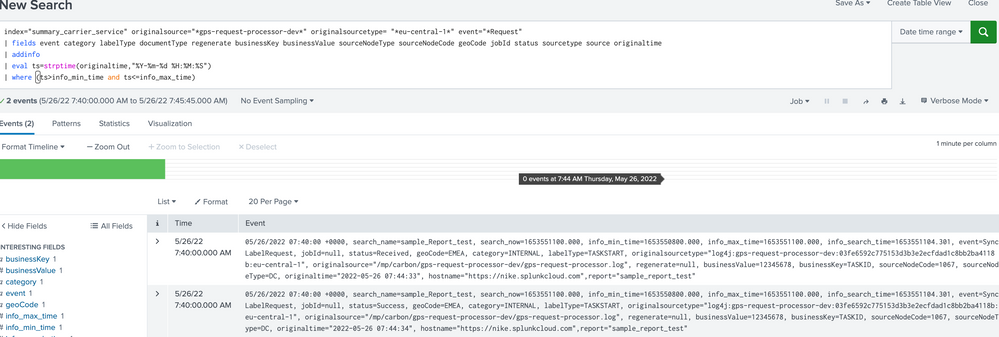
i found for below query the search is happening based on default time field which is _time , so when ever i am choosing the date and time based on default time which is '5/26/22 7:40:00.000 AM' then the events are populating but if i am selecting any date and time which is align with my custom time field which is 'originaltime' then i am not getting any event , am i doing any thing wrong here
index="summary_carrier_service" originalsource="*gps-request-processor-dev*" originalsourcetype= "*eu-central-1*" event="*Request"
| fields event category labelType documentType regenerate businessKey businessValue sourceNodeType sourceNodeCode geoCode jobId status sourcetype source originaltime
| addinfo
| eval ts=strptime(originaltime,"%Y-%m-%d %H:%M:%S")
| where (ts>info_min_time and ts<=info_max_time)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
richgalloway

SplunkTrust
05-26-2022
07:14 AM
The AND operator in the where command must be in upper case.
If you still don't get results, use the table command to examine the ts, info_min_time, and info_max_time fields.
---
If this reply helps you, Karma would be appreciated.
If this reply helps you, Karma would be appreciated.
Get Updates on the Splunk Community!
Prove Your Splunk Prowess at .conf25—No Prereqs Required!
Your Next Big Security Credential: No Prerequisites Needed
We know you’ve got the skills, and now, earning the ...
Splunk Observability Cloud's AI Assistant in Action Series: Observability as Code
This is the sixth post in the Splunk Observability Cloud’s AI Assistant in Action series that digs into how to ...
Splunk Answers Content Calendar, July Edition I
Hello Community!
Welcome to another month of Community Content Calendar series! For the month of July, we will ...