Join the Conversation
- Find Answers
- :
- Apps & Add-ons
- :
- All Apps and Add-ons
- :
- How to configure Splunk Supporting Add-on for Acti...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to configure Splunk Supporting Add-on for Active Directory on a single Splunk instance (running on Linux) for file upload?
I want to examine a snippet of AD logs (i.e. no real-time data) for testing on a Linux single-instance.
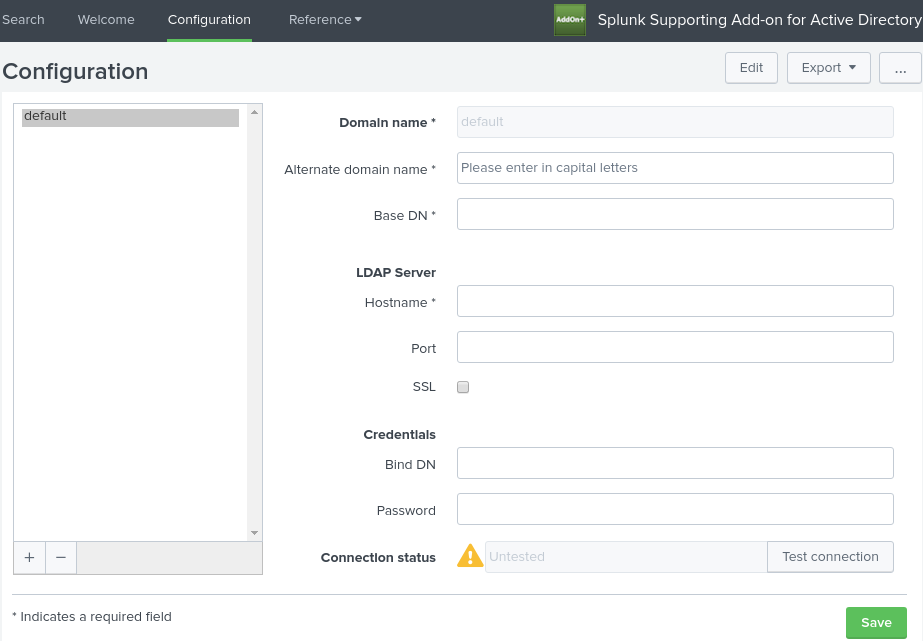
I installed the Splunk App for Windows Infrastructure which then prompted me to also install the Splunk Add-on for Microsoft Windows and Splunk Supporting Add-on for Microsoft Active Directory. Now to configure the AD Add-on, I need to fill in the below form:
I looked at this page: https://docs.splunk.com/Documentation/SA-LdapSearch/2.2.1/User/ConfiguretheSplunkSupportingAdd-onfor...
My understanding is that splunk would try to directly connect to the domain to monitor its AD data. But, I am provided with a snippet file of AD logs and should not monitor live data. How do I go about configuring the add-on/uploading the file in a readable format?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you can't connect to AD from the test server, using something like Logparser to convert to csv should do the trick.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @splunklearner1234,
The "Splunk Supporting Add-on for Microsoft Active Directory" allows you to fetch the AD objects such as users, assets, groups, etc... This is not for fetching AD logs, This is especially useful if you want to keep track of the AD tree since you'll be able to grab a daily snapshot and be able to compare and find out what has changed.
If you're looking for the TA to collect AD logs then you should be installing this on a UF on your AD server :
https://splunkbase.splunk.com/app/3207/
Let me know if you need more details.
Cheers,
David
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi David,
I am only working on a test server, with a snippet of existing log files which won't be updated for this purpose.
For this I will not be installing anything on the AD server itself, but I will be sent a file to use.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In that case for fetching the list of users, groups, etc.. "Splunk Supporting Add-on for Microsoft Active Directory" should do the trick, still have to connect from your test server to AD to get the tree, nothing to be installed on the AD server though. Hope this helps, and let us know what progress you've made.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I ended up using Microsoft Logparser to convert the files to csv before uploading, because there was no possibility to connect to AD from the test Splunk server. That seemed to work well without data loss.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Great to hear that 🙂