- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Why is the timechart coming up blank?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
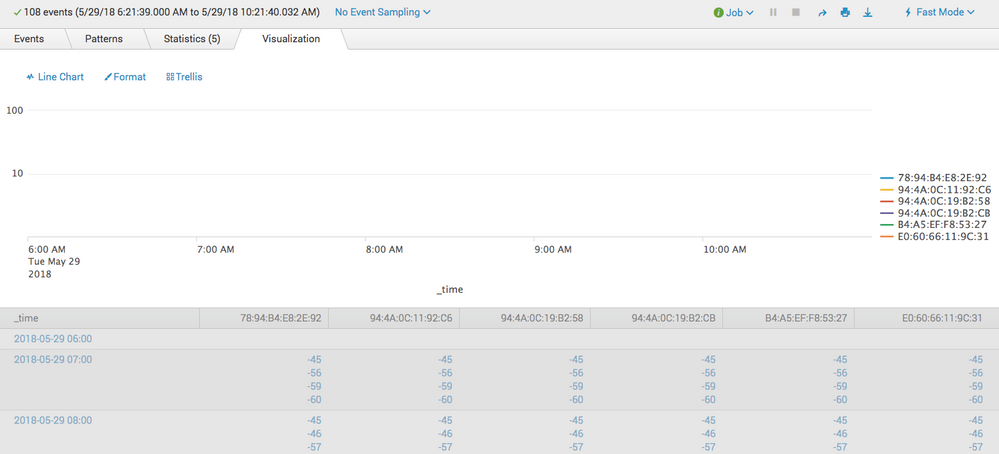
I have this query that works query wize but the resulting timechart is blank and I don't know why
earliest=-4hr index="camera_status" sourcetype=access_combined_camerastatus 8773|rex max_match=0 "Premise=\s+(?<premiseid>\d+)"|rex max_match=0 "Mac=\s+(?<macid>[a-fA-F0-9\.:-]{12,17})"|rex max_match=0 "RSSI=\s+(?<rssiid>[^\s]+)"|mvexpand rssiid|mvexpand macid|timechart span=1hr values(rssiid) by macid
Resulting timechart and data looks like the below.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you see it closely your values for each mac is multivalued field and thus considered as string, hence no chart data. Assuming macid and rssiid has one to one mapping, try something like this
earliest=-4hr index="camera_status" sourcetype=access_combined_camerastatus 8773|rex max_match=0 "Premise=\s+(?<premiseid>\d+)"|rex max_match=0 "Mac=\s+(?<macid>[a-fA-F0-9\.:-]{12,17})"|rex max_match=0 "RSSI=\s+(?<rssiid>[^\s]+)"
| eval temp=mvzip(macid,rssiid,"###") |mvexpand temp | rex field=temp "(?<macid>.+)###(?<rssiid>.+)"
|timechart span=1hr values(rssiid) by macid
Line three in above query converts two multivalued fields macid and rssiid in singular,one on one mapped, fields.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you see it closely your values for each mac is multivalued field and thus considered as string, hence no chart data. Assuming macid and rssiid has one to one mapping, try something like this
earliest=-4hr index="camera_status" sourcetype=access_combined_camerastatus 8773|rex max_match=0 "Premise=\s+(?<premiseid>\d+)"|rex max_match=0 "Mac=\s+(?<macid>[a-fA-F0-9\.:-]{12,17})"|rex max_match=0 "RSSI=\s+(?<rssiid>[^\s]+)"
| eval temp=mvzip(macid,rssiid,"###") |mvexpand temp | rex field=temp "(?<macid>.+)###(?<rssiid>.+)"
|timechart span=1hr values(rssiid) by macid
Line three in above query converts two multivalued fields macid and rssiid in singular,one on one mapped, fields.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ok first off, thank you! That worked!
would you mind walking me thru what this line is doing? I'll go read the docs as well but just so I can apply what you did to this query would be most helpful in framing it for me.
| eval temp=mvzip(macid,rssiid,"###") |mvexpand temp | rex field=temp "(?.+)###(?.+)"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Easiest way to seeing what each command does is to start off with below query and then start adding each search statement/segment one by one.
earliest=-4hr index="camera_status" sourcetype=access_combined_camerastatus 8773 | table _time _raw
Adding those rex statement would show you multivalued fields macid and rssiid extracted for each event.
Adding | eval temp=mvzip(macid,rssiid,"###") will create a new field, multivalued but each value is concatenation of value of fields macid and rssid, row by row within those multivalued field value.
e.g. (below is just one sample event)
macid rssid temp
mac1 rssiid1 mac1###rssiid1
mac2 rssiid2 mac2###rssiid2
...
The mvexpand temp will create a row for each value of multivalued field temp. The rex command will extract macid and rssid from field, which now will be singular fields. Then the timechart does what it should do.