- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Splunk query Optimize
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Why is the search with NOT take less time compared to search using IN?
Hello Everyone, I have two queries to exclude events one using NOT and other one using IN, both the queries returning same results but the query using NOT command takes less time.
My question is it should be other way around, why NOT is take less time to execute.
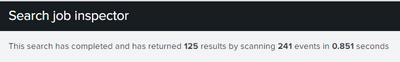
Time taken by Splunk using IN query
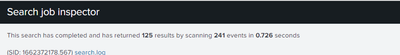
Time taken by Splunk using NOT query
index = "some_index" sourcetype="some_sourec_type" app_code=XXXX a_status IN (0,1,40) AND b_status IN (2,1,10,20)
index = "some_index" sourcetype="some_sourec_type" app_code=XXXX NOT a_status IN (0, -1, -2, -5) NOT b_status IN (-1, -6, -5, null)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @gcusello, 0 is in both the condition.
I executed the query yesterday and then today, it shows the same behavior.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Wonder_women,
zero in both conditions, means that the two searches have different results,
probably the zero condition matches many events and so the NOT conditions excludes more events, so in the result you have much less events so the results visualization is faster.
Try to use zero only in one of the searches.
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Wonder_women,
in general a NOT condition is always slower than an IN condition, so it's very strange your behavior.
Only two questions:
- the condition a_status=0 is in both the searches, it's a copy/past error, or it's present in bothe the searches?
- di you tried to execute the two searches in different times? in other words does the condition search_IN slower happen all the time or it's temporary?
Ciao.
Giuseppe