- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Why is Splunk gathering latest data even with Null...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
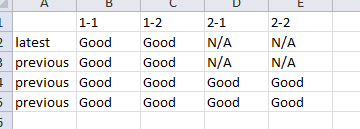
Why is Splunk gathering latest data even with Null values?
How can i get latest value of all ID (1-1,1-2,2-1,2-2). considering there are no latest data on ID(2-1,2-2)
Data:
12:10:01 ID 1-1, value="GOOD"
12:10:01 ID 1-2, value="GOOD"
12:10:02 ID 2-1, value="GOOD"
12:10:02 ID 2-2, value="GOOD"
12:10:03 ID 1-1, value="GOOD"
12:10:03 ID 1-2, value="GOOD"
12:10:04 ID 2-1, value="GOOD"
12:10:04 ID 2-2, value="GOOD"
12:10:05 ID 1-1, value="GOOD"
12:10:05 ID 1-2, value="GOOD"
12:10:06 ID 2-1, value="GOOD"
12:10:06 ID 2-2, value="GOOD"
12:10:07 ID 1-1, value="GOOD"
12:10:07 ID 1-2, value="GOOD"
12:10:08 ID 1-1, value="GOOD"
12:10:08 ID 1-2, value="GOOD"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm assuming your fields are extracted properly, so that "ID" and "value" are both extracted. You can retrieve the last value for each ID using the stats command latest:
[Your search string to find the events] | stats latest(value) by ID
This will give you a table of IDs and the latest value field for each. You can read more about stats here:
https://docs.splunk.com/Documentation/Splunk/latest/SearchReference/Stats