- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Why is MV_ADD=true extracting everything twice and...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
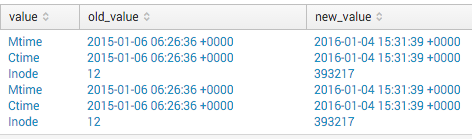
My Event:
Directory: /var/tmp/.X11-unix
Mtime : 2015-01-06 06:26:36 +0000 | 2016-01-04 15:31:39 +0000
Ctime : 2015-01-06 06:26:36 +0000 | 2016-01-04 15:31:39 +0000
Inode : 12 | 393217
Props.conf (the relevant stuff):
source::.../aide.log]
sourcetype = aide
#Configuration for the new sourcetype
[aide]
pulldown_type = TRUE
SHOULD_LINEMERGE = TRUE
MAX_EVENTS = 1000
KV_MODE = none
DATETIME_CONFIG = NONE
MAX_TIMESTAMP_LOOKAHEAD = 0
REPORT-extract_changes = extract_changes
Transforms:
#Extract each field pair from detailed message:
[extract_changes]
REGEX = ^\s\s(\w+)\s*:\s([^|]+)\|\s([^\n]+)\n*
FORMAT = value::$1 old_value::$2 new_value::$3
MV_ADD=true
These give me twice the results I would expect, can't figure out why:
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I feel kind of stupid now, but the issue was with my original search, I had been using:
Wrong Search:
index="aide_index" | extract reload=t | search "Socket" | table _time _raw, value, old_value, new_value
Correct Search:
index="aide_index" | search "Socket" | table _time _raw, value, old_value, new_value
I forgot to remove extract reload=t after refreshing the new transforms.conf file... so it was parsing all those fields twice.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What is the search you are using to produce the results?
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I feel kind of stupid now, but the issue was with my original search, I had been using:
Wrong Search:
index="aide_index" | extract reload=t | search "Socket" | table _time _raw, value, old_value, new_value
Correct Search:
index="aide_index" | search "Socket" | table _time _raw, value, old_value, new_value
I forgot to remove extract reload=t after refreshing the new transforms.conf file... so it was parsing all those fields twice.