- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Users loging into workstations with local admin or...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Users loging into workstations with local admin or domain admin privs
First off, I am very new to Splunk and that may be my downfall. Our latest Splunk guru has left and this fell to me rather abruptly, so I apologize in advance.
I have been tasked with generating a report showing users that are logging into the local computers with elevated privileges of their standard daily accounts.
For example, if a user has two logins, username and ADUserName. I need to find out if username is a local admin on their computer and when they have logged in using that account.
I have been trying to figure this out but for the last two weeks haven't actually made any progress.
Hoping someone can point me in the right direction - thank you very much!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are you collecting logs from endpoints to see if user is making login locally instead using his/her domain account.
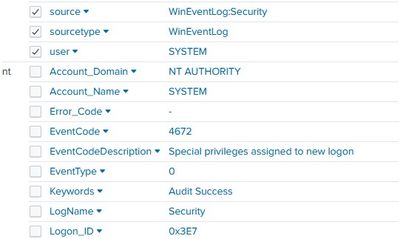
You need to have event logs from each endpoint to detect if they are login locally using admin rights. 4672 is the event code.
https://www.ultimatewindowssecurity.com/securitylog/encyclopedia/event.aspx?eventID=4672
or you could easily detect employees who are login using local admin account if you have Microsoft defender ATP installed on endpoints.
If this helps, give a like below.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We are ingesting those logs from all the end points.
I have searched on that and am only finding systems logging in with elevated privs. I know the admins are doing this, they will tell me they are, but looking for a way to see the activity 😞
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did you see 4672 events collected from endpoints?
If this helps, give a like below.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, I do see 4672 from end points.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you try accessing endpoint using local admin account and see how events is generated then you can understand event behavior.
If this helps, give a like below.