- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Timechart count by ip by fw_name over time wit...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm trying to build a search that displays the count of individual source IP addresses based on some criteria for each firewall. Below is the closest I've been able to get. I've tried about 15 variations of | stats, | chart and | timechart combinations for this. The goal is to get a line graph of each count of source IP addresses in a trellis separated by firewall name. Instead of seeing the total count as the timechart below displays.
| timechart count(ip) by fw_name
I'm looking for a '| timechart count by ip' style output but with trellises separated by fw_name. After hours of searching I'm not sure it's doable.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@nsnelson402 you can try bin command on _time and then use stats for the correlation with multiple fields including time. Finally use eval {field}=aggregation to get it Trellis ready.
In your case try the following (span is 1h in example, but it can be made dynamic based on time input, but keeping example simple):
<yourCurrentSearch>
| bin _time span=1h
| stats count by _time ip fw_name
| eval {fw_name}=count
| fields - fw_name count
Then choose the aggregation as you want to split through Trellis
Following is a run anywhere example based on Splunk's _internal index:
index=_internal sourcetype=splunkd
| bin _time span=5min
| stats count by _time component log_level
| eval {log_level}=count
| fields - log_level count
Following is the Simple XML Code for attached screenshot that you can play with.
<dashboard theme="dark">
<label>Trellis with Time and Two aggregation</label>
<row>
<panel>
<chart>
<search>
<query>index=_internal sourcetype=splunkd
| bin _time span=5min
| stats count by _time component log_level
| eval {log_level}=count
| fields - log_level count</query>
<earliest>-60min</earliest>
<latest>now</latest>
<sampleRatio>1</sampleRatio>
</search>
<option name="charting.axisLabelsX.majorLabelStyle.overflowMode">ellipsisNone</option>
<option name="charting.axisLabelsX.majorLabelStyle.rotation">0</option>
<option name="charting.axisTitleX.visibility">collapsed</option>
<option name="charting.axisTitleY.visibility">collapsed</option>
<option name="charting.axisTitleY2.visibility">collapsed</option>
<option name="charting.axisX.abbreviation">none</option>
<option name="charting.axisX.scale">linear</option>
<option name="charting.axisY.abbreviation">none</option>
<option name="charting.axisY.scale">linear</option>
<option name="charting.axisY2.abbreviation">none</option>
<option name="charting.axisY2.enabled">0</option>
<option name="charting.axisY2.scale">inherit</option>
<option name="charting.chart">line</option>
<option name="charting.chart.bubbleMaximumSize">50</option>
<option name="charting.chart.bubbleMinimumSize">10</option>
<option name="charting.chart.bubbleSizeBy">area</option>
<option name="charting.chart.nullValueMode">zero</option>
<option name="charting.chart.showDataLabels">none</option>
<option name="charting.chart.sliceCollapsingThreshold">0.01</option>
<option name="charting.chart.stackMode">default</option>
<option name="charting.chart.style">shiny</option>
<option name="charting.drilldown">none</option>
<option name="charting.layout.splitSeries">0</option>
<option name="charting.layout.splitSeries.allowIndependentYRanges">0</option>
<option name="charting.legend.labelStyle.overflowMode">ellipsisMiddle</option>
<option name="charting.legend.mode">seriesCompare</option>
<option name="charting.legend.placement">none</option>
<option name="charting.lineWidth">2</option>
<option name="height">575</option>
<option name="refresh.display">progressbar</option>
<option name="trellis.enabled">1</option>
<option name="trellis.scales.shared">0</option>
<option name="trellis.size">medium</option>
<option name="trellis.splitBy">log_level</option>
</chart>
</panel>
</row>
</dashboard>
| makeresults | eval message= "Happy Splunking!!!"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@nsnelson402 you can try bin command on _time and then use stats for the correlation with multiple fields including time. Finally use eval {field}=aggregation to get it Trellis ready.
In your case try the following (span is 1h in example, but it can be made dynamic based on time input, but keeping example simple):
<yourCurrentSearch>
| bin _time span=1h
| stats count by _time ip fw_name
| eval {fw_name}=count
| fields - fw_name count
Then choose the aggregation as you want to split through Trellis
Following is a run anywhere example based on Splunk's _internal index:
index=_internal sourcetype=splunkd
| bin _time span=5min
| stats count by _time component log_level
| eval {log_level}=count
| fields - log_level count
Following is the Simple XML Code for attached screenshot that you can play with.
<dashboard theme="dark">
<label>Trellis with Time and Two aggregation</label>
<row>
<panel>
<chart>
<search>
<query>index=_internal sourcetype=splunkd
| bin _time span=5min
| stats count by _time component log_level
| eval {log_level}=count
| fields - log_level count</query>
<earliest>-60min</earliest>
<latest>now</latest>
<sampleRatio>1</sampleRatio>
</search>
<option name="charting.axisLabelsX.majorLabelStyle.overflowMode">ellipsisNone</option>
<option name="charting.axisLabelsX.majorLabelStyle.rotation">0</option>
<option name="charting.axisTitleX.visibility">collapsed</option>
<option name="charting.axisTitleY.visibility">collapsed</option>
<option name="charting.axisTitleY2.visibility">collapsed</option>
<option name="charting.axisX.abbreviation">none</option>
<option name="charting.axisX.scale">linear</option>
<option name="charting.axisY.abbreviation">none</option>
<option name="charting.axisY.scale">linear</option>
<option name="charting.axisY2.abbreviation">none</option>
<option name="charting.axisY2.enabled">0</option>
<option name="charting.axisY2.scale">inherit</option>
<option name="charting.chart">line</option>
<option name="charting.chart.bubbleMaximumSize">50</option>
<option name="charting.chart.bubbleMinimumSize">10</option>
<option name="charting.chart.bubbleSizeBy">area</option>
<option name="charting.chart.nullValueMode">zero</option>
<option name="charting.chart.showDataLabels">none</option>
<option name="charting.chart.sliceCollapsingThreshold">0.01</option>
<option name="charting.chart.stackMode">default</option>
<option name="charting.chart.style">shiny</option>
<option name="charting.drilldown">none</option>
<option name="charting.layout.splitSeries">0</option>
<option name="charting.layout.splitSeries.allowIndependentYRanges">0</option>
<option name="charting.legend.labelStyle.overflowMode">ellipsisMiddle</option>
<option name="charting.legend.mode">seriesCompare</option>
<option name="charting.legend.placement">none</option>
<option name="charting.lineWidth">2</option>
<option name="height">575</option>
<option name="refresh.display">progressbar</option>
<option name="trellis.enabled">1</option>
<option name="trellis.scales.shared">0</option>
<option name="trellis.size">medium</option>
<option name="trellis.splitBy">log_level</option>
</chart>
</panel>
</row>
</dashboard>
| makeresults | eval message= "Happy Splunking!!!"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I've just come acroos this post and your trellised charts are very similar to something I am tryng the achieve.
I am new to Splunk and so may be missing something, but I can;t replicate your layout. - is the XML you posted necessary to get the layout you have?
This is my search:
index=felix_emea sourcetype="Felixapps:prod:log" Action = "Resp_VPMG"
| dedup EventIndex
| rex field=Message "^<b>(?<Region>.+)<\/b>"
| rex "Response Codes:\s(?<responseCode>\d{1,3})"
| rex field=Message ":\s(?<errCount>\d{1,4})$"
| bin _time span=1h
| stats count by _time, Region, responseCode
| eval {responseCode}=count
| fields - responseCode, region, count
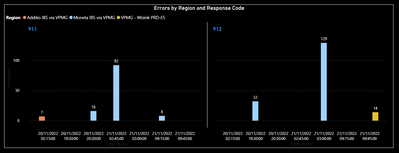
This is a sample of my data:
Time | responseCode | Region | errCount |
21/11/2022 09:46:07 | 912 | VPMG - Wizink PRD-E5 | 14 |
| 21/11/2022 09:16:31 | 911 | Moneta IBS via VPMG | 8 |
| 21/11/2022 03:02:07 | 912 | Moneta IBS via VPMG | 129 |
| 21/11/2022 02:46:59 | 911 | Moneta IBS via VPMG | 92 |
| 20/11/2022 20:31:38 | 911 | Moneta IBS via VPMG | 16 |
| 20/11/2022 19:31:36 | 912 | Moneta IBS via VPMG | 32 |
| 20/11/2022 02:26:45 | 911 | Addiko IBS via VPMG | 7 |
and this is the visualisation I'm trying to acheive (this is done in Power BI):
Is this achieveable in Splunk?
Thanks,
Steve
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
OK,
I think I've gotten there with this search:
index=felix_emea sourcetype="Felixapps:prod:log" Action = "Resp_VPMG"
| dedup EventIndex
| rex field=Message "^<b>(?<Region>.+)<\/b>"
| rex "Response Codes:\s(?<responseCode>\d{1,3})"
| rex field=Message ":\s(?<errCount>\d{1,4})$"
| bin _time span=1h
| stats count by _time responseCode Region
| eval {Region}=count
| fields - count
Can you tell me the purpose of thise line in your code:
| fields - log_level count
as to me that drops the 'count' and 'log_level' fields yet log_level is a value you are trying to chart.
Thanks,
Steve
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I tweaked it a little bit, but this is exactly what I was looking for, thank you so much.
| bin _time span=1h
| stats count by _time fw_name ip
| eval {ip}=count
| fields - ip count
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
with trellis
please make dashboard and panel.
each fw_name panel can use with trellis
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm not looking to have a trellis for each source IP on different panels for each firewall. The application of this search could be used for many dynamic scenarios and building a dashboard with multiple panels each time is cumbersome.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
trellis can't work both ip and fw_name