- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Splunk query to eliminate specific events
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Splunk query to eliminate specific events
Hi,
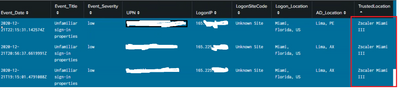
Below is my splunk search query & Screenshot. I want eliminate TrustedLocation = "Zscaler Miami III" from my result.
Please help me with splunk query. I tried but unable to acheive it.
index=test "vendorInformation.provider"=IPC
| eval Event_Date=mvindex('eventDateTime',0)
| eval UPN=mvindex('userStates{}.userPrincipalName',0)
| eval Logon_Location=mvindex('userStates{}.logonLocation',0)
| eval Event_Title=mvindex('title',0)
| eval Event_Severity=mvindex('severity',0)
| eval AAD_Acct=mvindex('userStates{}.aadUserId',0)
| eval LogonIP=mvindex('userStates{}.logonIp',0)
| eval Investigate=+"https://portal.azure.com/#blade/Microsoft_AAD_IAM/RiskyUsersBlade/userId/".AAD_Acct
| stats count by Event_Date, Event_Title, Event_Severity UPN Logon_Location LogonIP Investigate
| lookup WeirMFAStatusLookup.csv userPrincipalName as UPN
| lookup Lookup_EMPADInfo.csv userPrincipalName as UPN
| lookup WeirSiteCode2IP.csv public_ip as LogonIP
| lookup ZscalerIP CIDR_IP as LogonIP
| lookup WeirTrustedIPs.csv TrustedIP as LogonIP
| fillnull value="Unknown Site" site_code
| eval AD_Location=st + ", " + c
| fillnull value="OK" MFAStatus
| eval TrustedLocation=if(isnull(TrustedLocation), ZLocation, TrustedLocation)
| rename site_code as LogonSiteCode
| table Event_Date, Event_Title, Event_Severity UPN LogonIP LogonSiteCode Logon_Location AD_Location TrustedLocation MFAStatus count Investigate
| sort - Event_Date
@soutamo @ITWhisperer @gcusello @thambisetty @richgalloway @to4kawa
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@saravanan90 Thanks for your reply.
Search result's count is mismatching.
It should give 45 counts without "Zscaler Miami III "but i am getting only 30 values as result.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Check if the below works.
| makeresults count=10| streamstats count| eval TrustedLocation="Zscaler Miami III"| eval TrustedLocation=if(count%2=0,TrustedLocation,"otherdata") | search TrustedLocation!="Zscaler Miami III"
-----------------------------------------
An upvote would be appreciated if the above reply is useful to you.