- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: [SmartStore] How to map report acceleration re...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
[SmartStore] How to map report acceleration report with the corresponding buckets?
After Smartstore was enabled for deployment the indexer's log's are flooded with messages like
"INFO CacheManagerHandler - cache_id="ra|tto_uswest2_tomcatfrontend~39~4345D76C-80D6-4BC7-991F-EA835C2B892C|08281223-D92B-4A36-BCA0-83970376D322_tto_search_agupta13_NS2480590abee10f99" not found
cache_id = ra|tto_uswest2_tomcatfrontend~39~4345D76C-80D6-4BC7-991F-EA835C2B892C|"
What the best way to find teh bucket corresponding to report acceleration.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We have a lot of similar "not found" messages flooding from CacheManagerHandler for dma buckets on the indexers logs. Splunk working on single-site indexer cluster. Since these logs are INFO, is this normal behavior or what should we check?
Thank you in advance
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
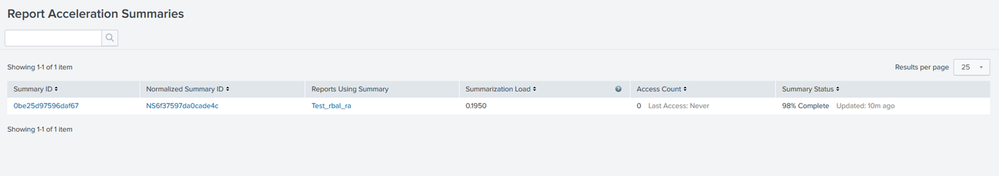
Here are the steps that can be used to check the Report acceleration and the corresponding bucket upload to the remote store.
OR else you could also use the REST endpoint
|rest /servicesNS/-/-/admin/summarization splunk_server=local | table summary.hash,summary.id,summary.is_inprogress,summary.size,summary.time_range, summary.complete,saved_searches.admin;search;*
Normalized Summary Id=NS6f37597da0cade4c” as would match with the name highlighted below in the bucket path.
$SPLUNK_HOME/bin/splunk cmd splunkd rfs -- ls --starts-with volume:my_s3_vol | grep -i '/ra/'
4220,_internal/ra/0c/a8/26~949FE8DD-2419-4F07-A151-77B02413A437/3F3F537C-7DAD-4CF8-B062-168D17BC15C7_search_admin_NS6f37597da0cade4c/guidSplunk-949FE8DD-2419-4F07-A151-77B02413A437/metadata
75,_internal/ra/0c/a8/26~949FE8DD-2419-4F07-A151-77B02413A437/3F3F537C-7DAD-4CF8-B062-168D17BC15C7_search_admin_NS6f37597da0cade4c/guidSplunk-949FE8DD-2419-4F07-A151-77B02413A437/metadata_c
71680,_internal/ra/0c/a8/26~949FE8DD-2419-4F07-A151-77B02413A437/3F3F537C-7DAD-4CF8-B062-168D17BC15C7_search_admin_NS6f37597da0cade4c/guidSplunk-949FE8DD-2419-4F07-A151-77B02413A437/ra_data
799,_internal/ra/0c/a8/26~949FE8DD-2419-4F07-A151-77B02413A437/3F3F537C-7DAD-4CF8-B062-168D17BC15C7_search_admin_NS6f37597da0cade4c/receipt.json
4220,_internal/ra/37/73/28~949FE8DD-2419-4F07-A151-77B02413A437/3F3F537C-7DAD-4CF8-B062-168D17BC15C7_search_admin_NS6f37597da0cade4c/guidSplunk-949FE8DD-2419-4F07-A151-77B02413A437/metadata
75,_internal/ra/37/73/28~949FE8DD-2419-4F07-A151-77B02413A437/3F3F537C-7DAD-4CF8-B062-168D17BC15C7_search_admin_NS6f37597da0cade4c/guidSplunk-949FE8DD-2419-4F07-A151-77B02413A437/metadata_c
71680,_internal/ra/37/73/28~949FE8DD-2419-4F07-A151-77B02413A437/3F3F537C-7DAD-4CF8-B062-168D17BC15C7_search_admin_NS6f37597da0cade4c/guidSplunk-949FE8DD-2419-4F07-A151-77B02413A437/ra_data
799,_internal/ra/37/73/28~949FE8DD-2419-4F07-A151-77B02413A437/3F3F537C-7DAD-4CF8-B062-168D17BC15C7_search_admin_NS6f37597da0cade4c/receipt.json
6294,_internal/ra/3c/fd/27~DA6E5901-FAF9-4AC1-855C-8C5E53A87B23/3F3F537C-7DAD-4CF8-B062-168D17BC15C7_search_admin_NS6f37597da0cade4c/guidSplunk-949FE8DD-2419-4F07-A151-77B02413A437/metadata