Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Splunk Search
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Multiple values - mvexpand not doing what I expect
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
dbcase
Motivator
02-19-2018
11:44 AM
Hi ,
I have a query that looks like this
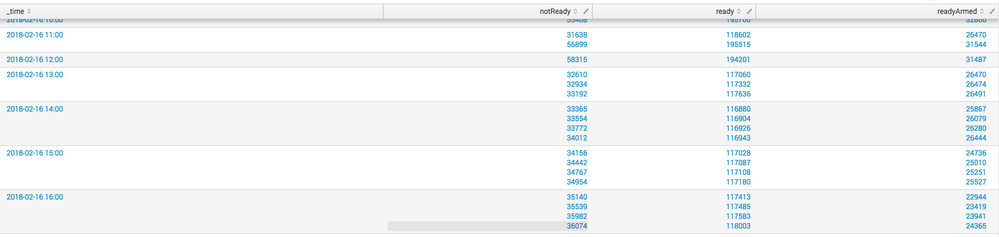
earliest=-100hr index=blahalarm STATUS=readyArmed OR STATUS=ready OR STATUS=notReady|mvexpand notReady|mvexpand ready|mvexpand readyArmed|mvexpand _time|timechart span=1hr values(field2) by STATUS
but the resulting dataset comes back as this. I'm confused, why wouldn't mvexpand create multiple events?
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
dbcase
Motivator
02-19-2018
11:55 AM
FIxed it. My data was coming in with 15min increments but my span=1hr, once I set my span to 15min all is well
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
dbcase
Motivator
02-19-2018
11:55 AM
FIxed it. My data was coming in with 15min increments but my span=1hr, once I set my span to 15min all is well
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
elliotproebstel
Champion
02-19-2018
11:54 AM
Doesn't the final timechart span=1h bring the events back into 1h buckets? The result looks like what I'd expect. Can you say more about what you're trying to achieve?
Get Updates on the Splunk Community!
Announcing Scheduled Export GA for Dashboard Studio
We're excited to announce the general availability of Scheduled Export for Dashboard Studio. Starting in ...
Extending Observability Content to Splunk Cloud
Watch Now!
In this Extending Observability Content to Splunk Cloud Tech Talk, you'll see how to leverage ...
More Control Over Your Monitoring Costs with Archived Metrics GA in US-AWS!
What if there was a way you could keep all the metrics data you need while saving on storage costs?This is now ...